Wireless Network Security Incident Response: Strategies for a Secure Environment
Introduction
In today's rapidly evolving digital landscape, wireless network security is a top concern for businesses and organizations. With the increasing reliance on wireless networks for communication and data transmission, the risks associated with unauthorized access, data breaches, and malware attacks have grown exponentially. A robust incident response plan is essential to detect, respond to, and recover from such incidents, minimizing downtime and data loss. In this article, we will explore the importance of wireless network security incident response and discuss strategies for managing wireless network security incidents.Understanding Wireless Network Security Incident Response
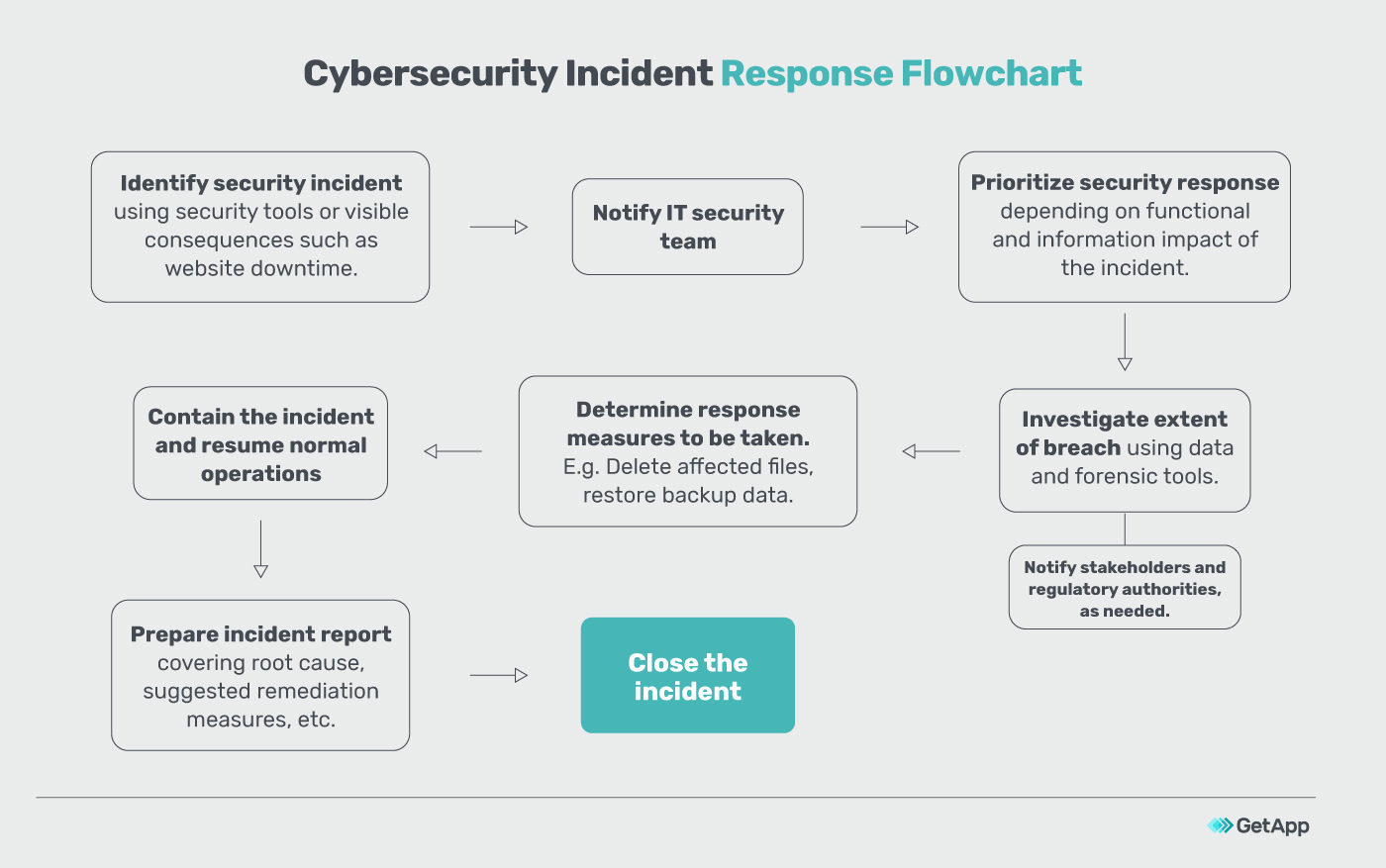
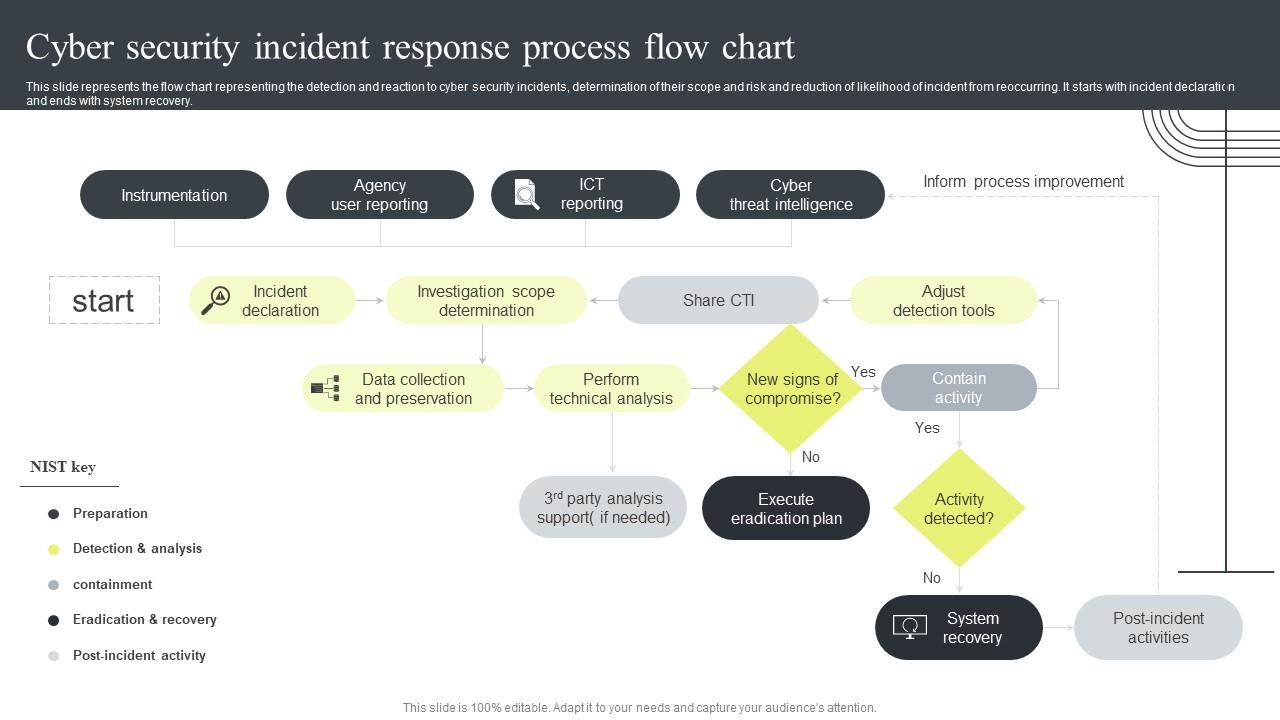
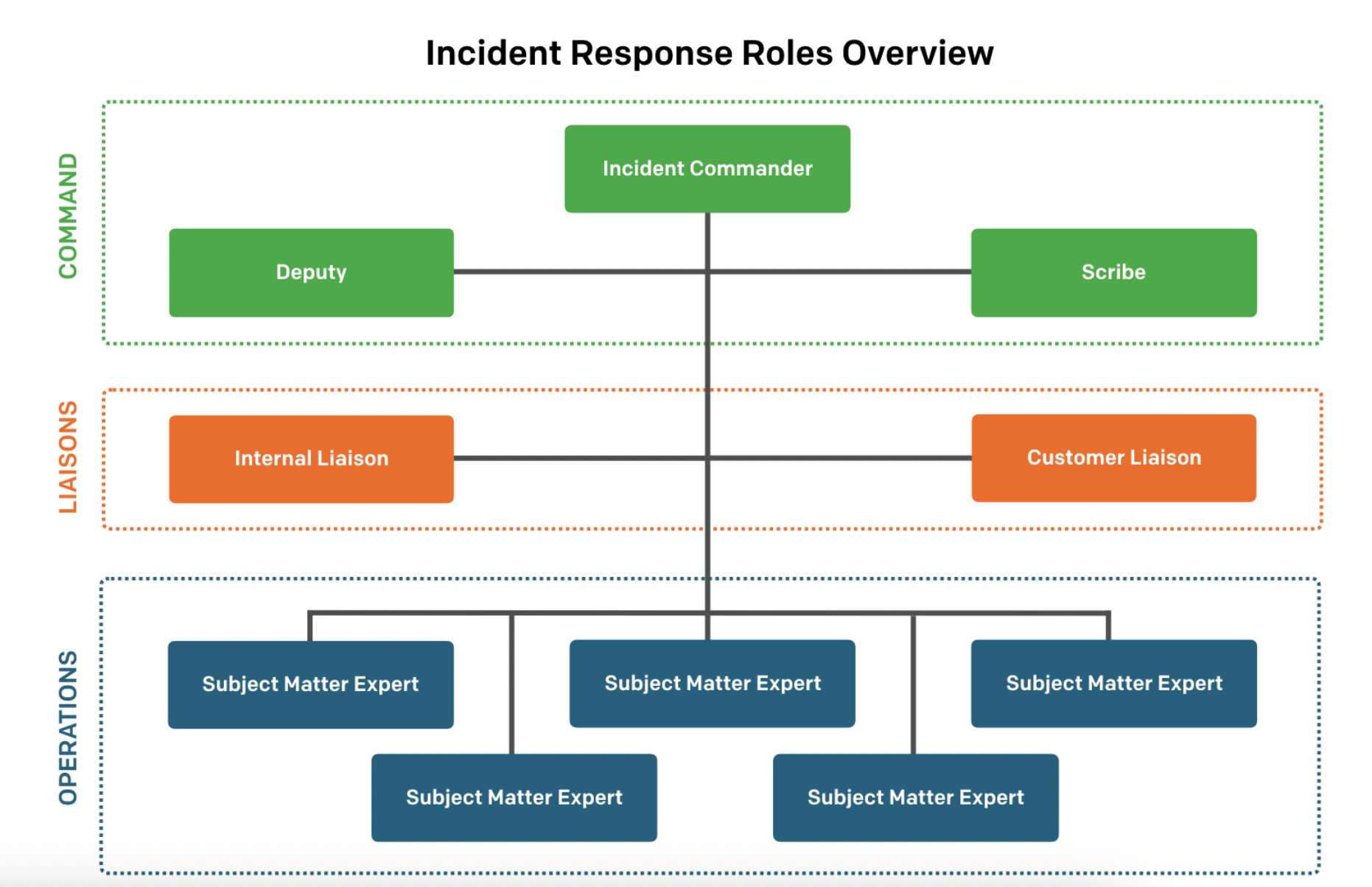
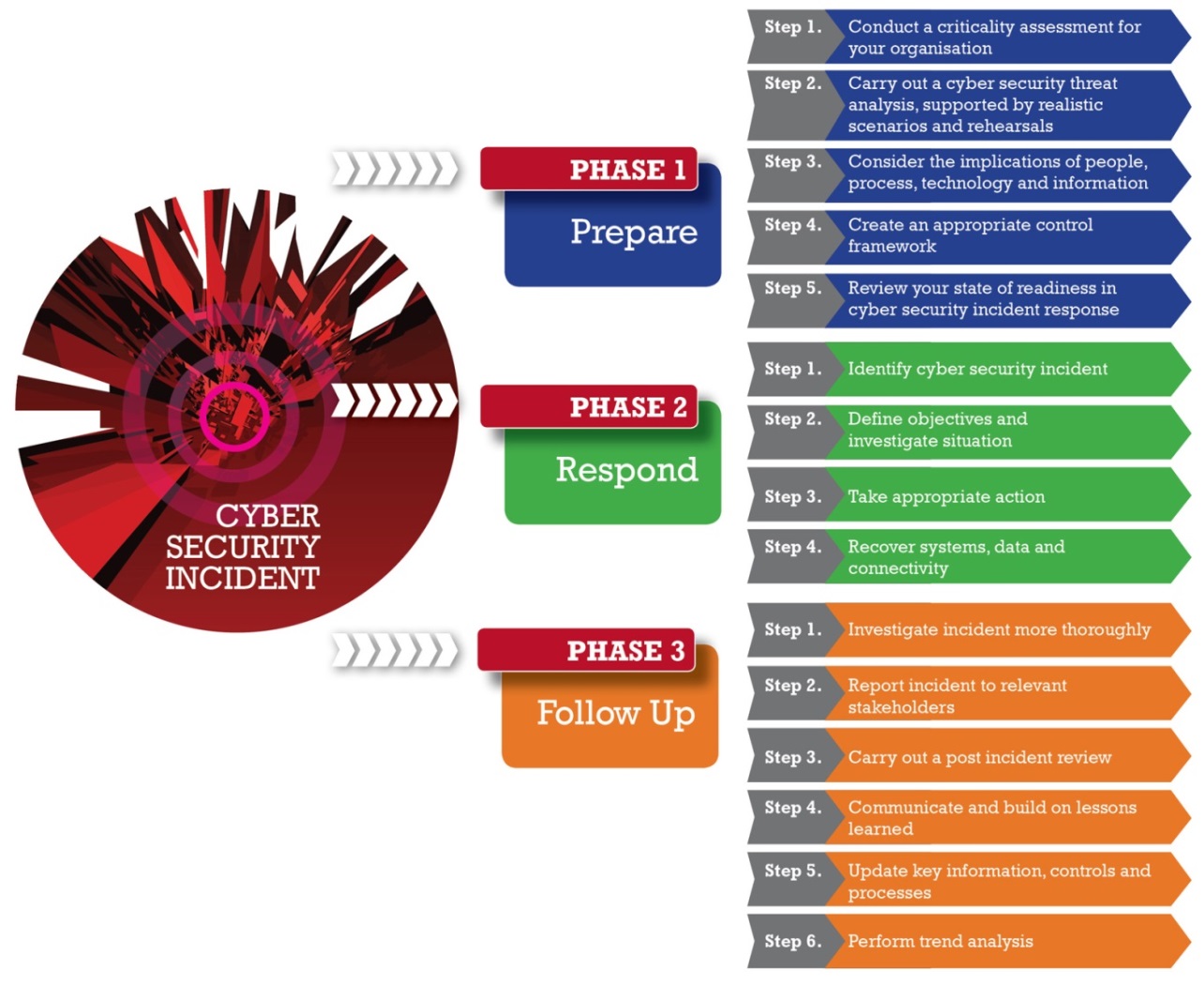
Wireless network security incident response is a set of instructions that help IT teams detect, respond to, and recover from incidents like cybercrime, data loss, and service outages that threaten daily workflow. A well-structured incident response plan is critical to minimizing the impact of such incidents and ensuring the continuity of business operations. The plan should include procedures for detection, containment, eradication, recovery, and post-incident activities.Detection and Containment
The first step in responding to a wireless network security incident is detection. This involves monitoring network traffic to identify unusual patterns or suspicious activity. Once an incident is detected, containment measures must be implemented to prevent the spread of the malware or unauthorized access to sensitive data. This may involve isolating the affected area or disconnecting the network.Containment and Eradication
After containment, the focus shifts to eradication. This involves identifying and neutralizing the root cause of the incident, which may involve identifying and removing malicious scripts or software from the network. The IT support team plays a crucial role in implementing technical recovery measures and restoring systems to normal functioning.Recovery and Post-Incident Activities