Secure Online Data Removal Techniques: Protect Your Digital Identity
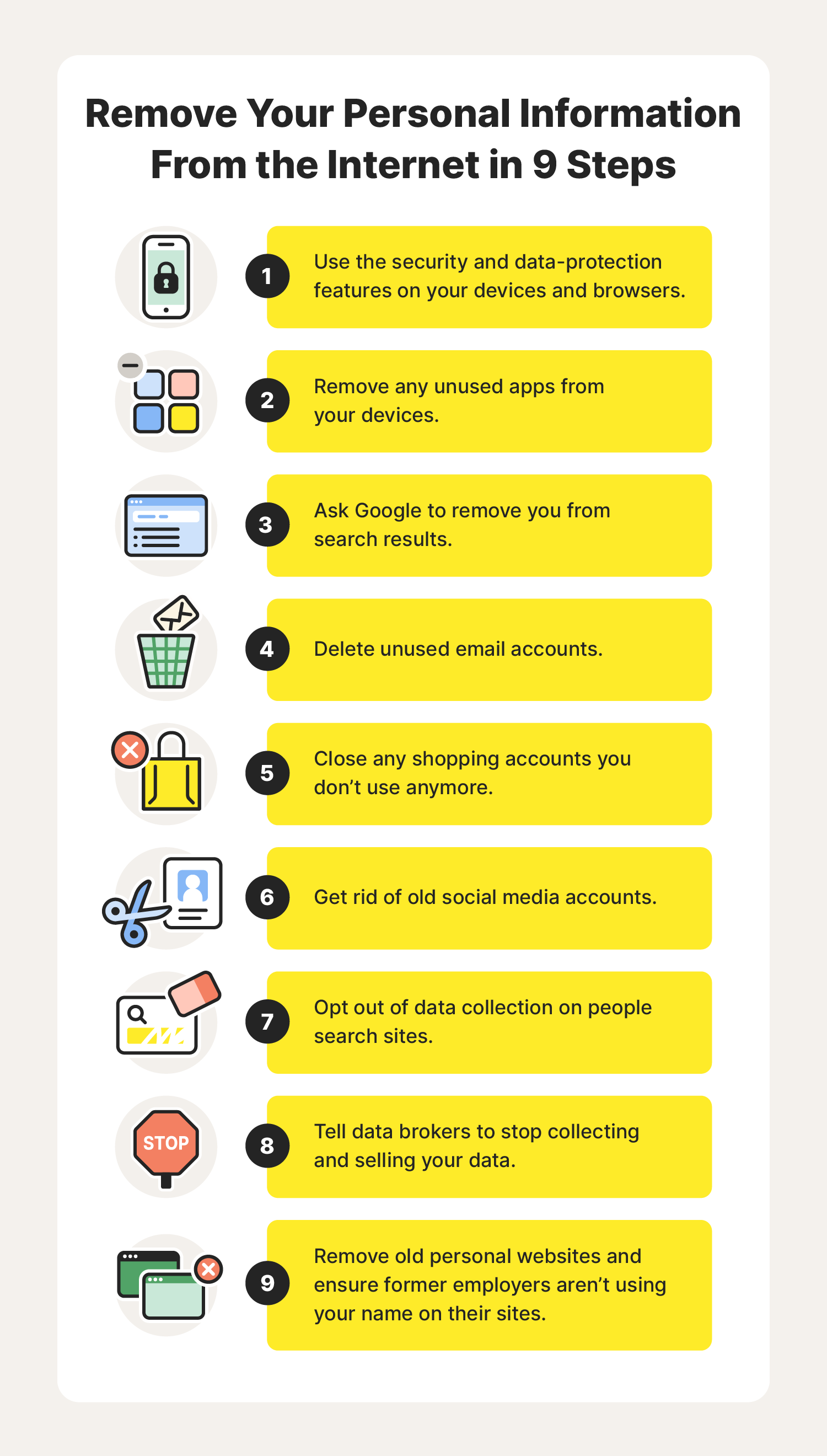
Data aggregators gather and sell personal information on the web, compromising individual privacy. Secure online data removal techniques can help erase and limit online presence, safeguarding against data brokers and identity theft.
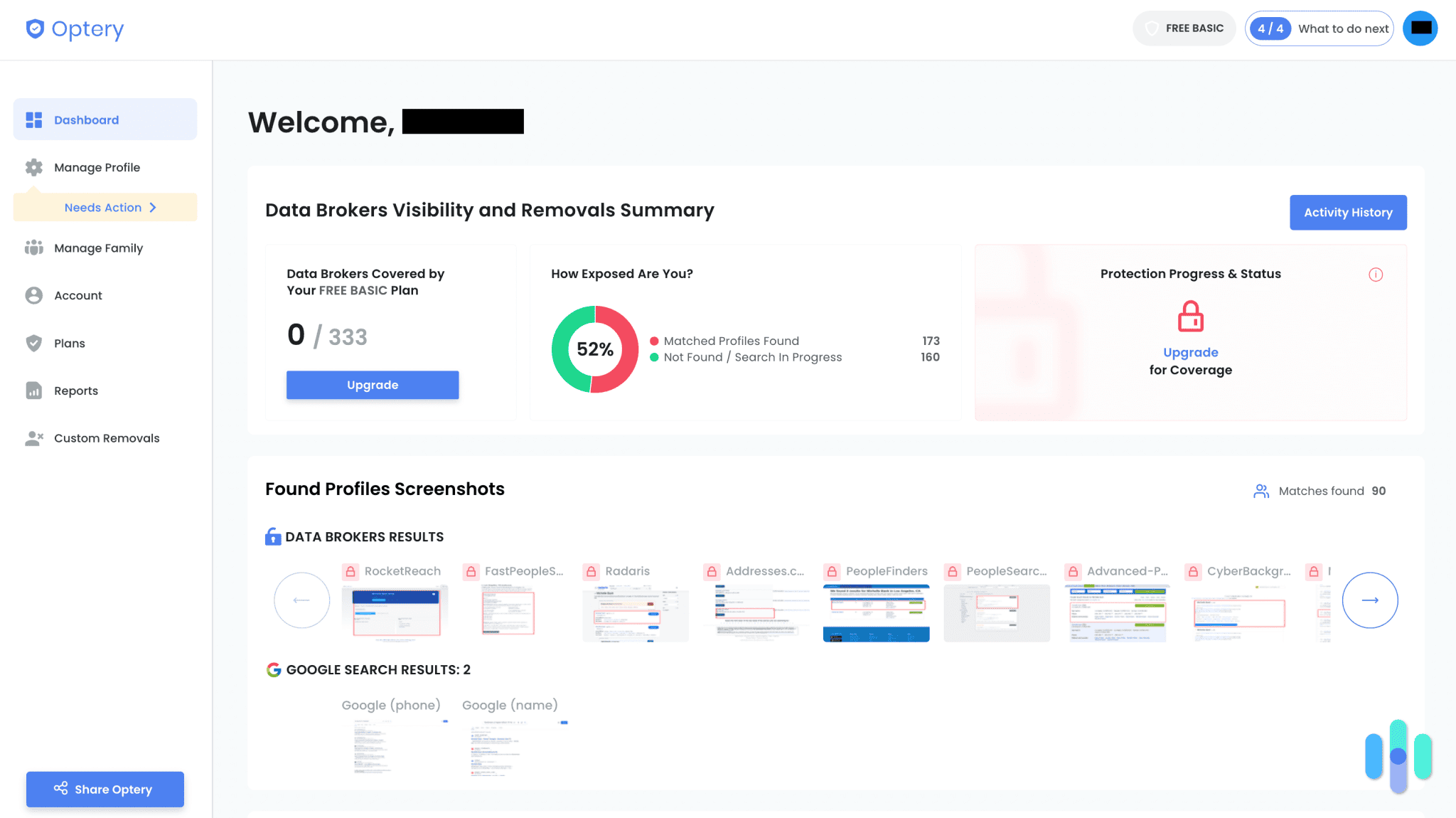
Top Personal Data Removal Services
- Incogni: Offers comprehensive protection with unlimited custom removals and real-time antivirus protection.
- Aura: Provides data removal from over 200 broker sites, people-search sites, credit solicitors, and junk mailers, along with online and device security tools.
Secure Data Disposal Methods
Secure data disposal is critical, especially when sensitive data is stored by organizations. Various data deletion methods are available, each with its own unique benefits and requirements:
- Secure Deletion: Refers to the process of deleting sensitive data in a way that it becomes irretrievable.
- Wiping: Overwrites data with random patterns to make it unreadable and irretrievable.
- Degaussing: Uses a strong magnetic field to demagnetize data, making it impossible to recover.
- Shredding: Physically shreds data storage devices to prevent unauthorized access.
- Erasure: Removes sensitive data from digital devices and storage media.
Types of Data Deletion
Entities must comply with equipment and data disposal policies. There are multiple types of data destruction methods:
- Physical Destruction: Physically destroys data storage devices to prevent unauthorized access.
- Electronic Destruction: Uses software or hardware to erase data, making it irretrievable.
- Secure Erasure: Removes sensitive data from digital devices and storage media using secure methods.
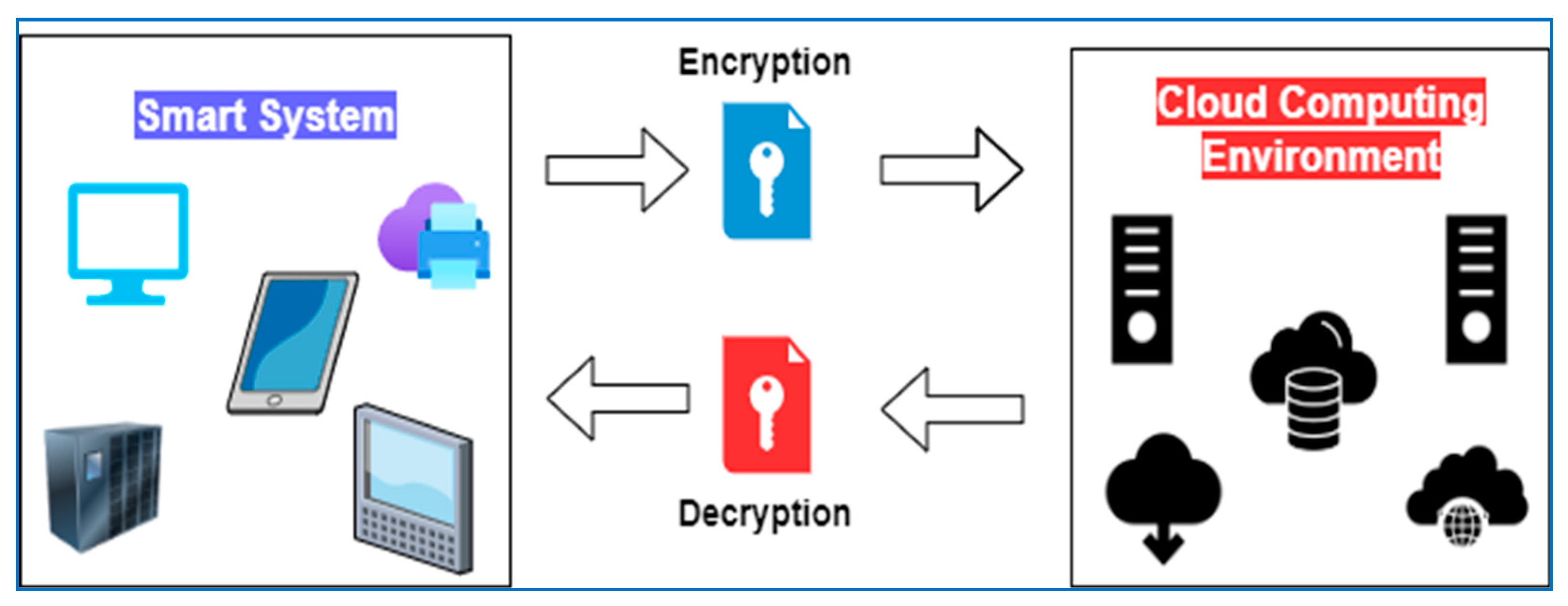
Secure Online Data Removal Techniques
Secure online data removal techniques involve using third-party services or software to erase and limit online presence. This includes:
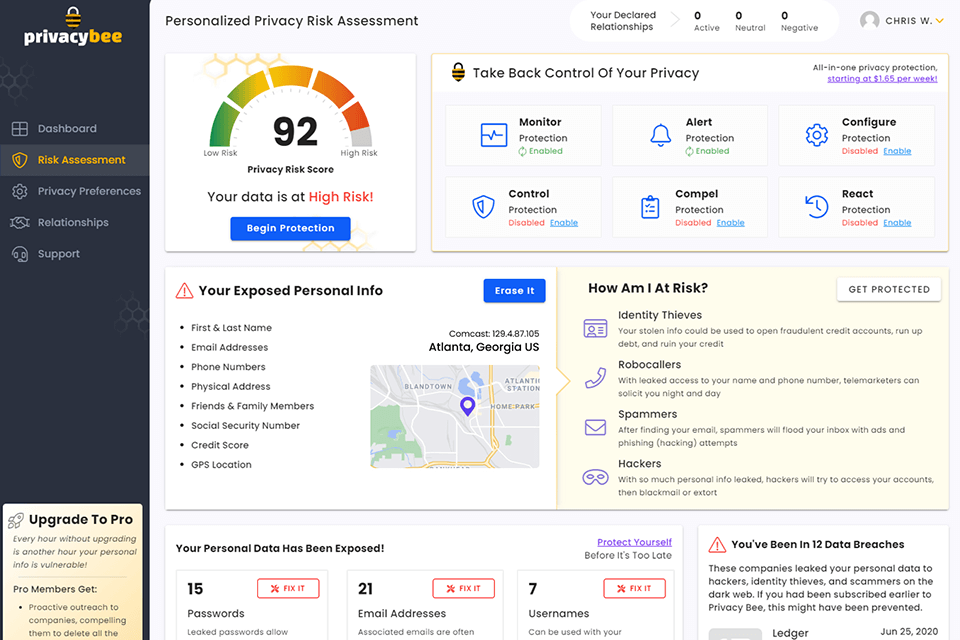
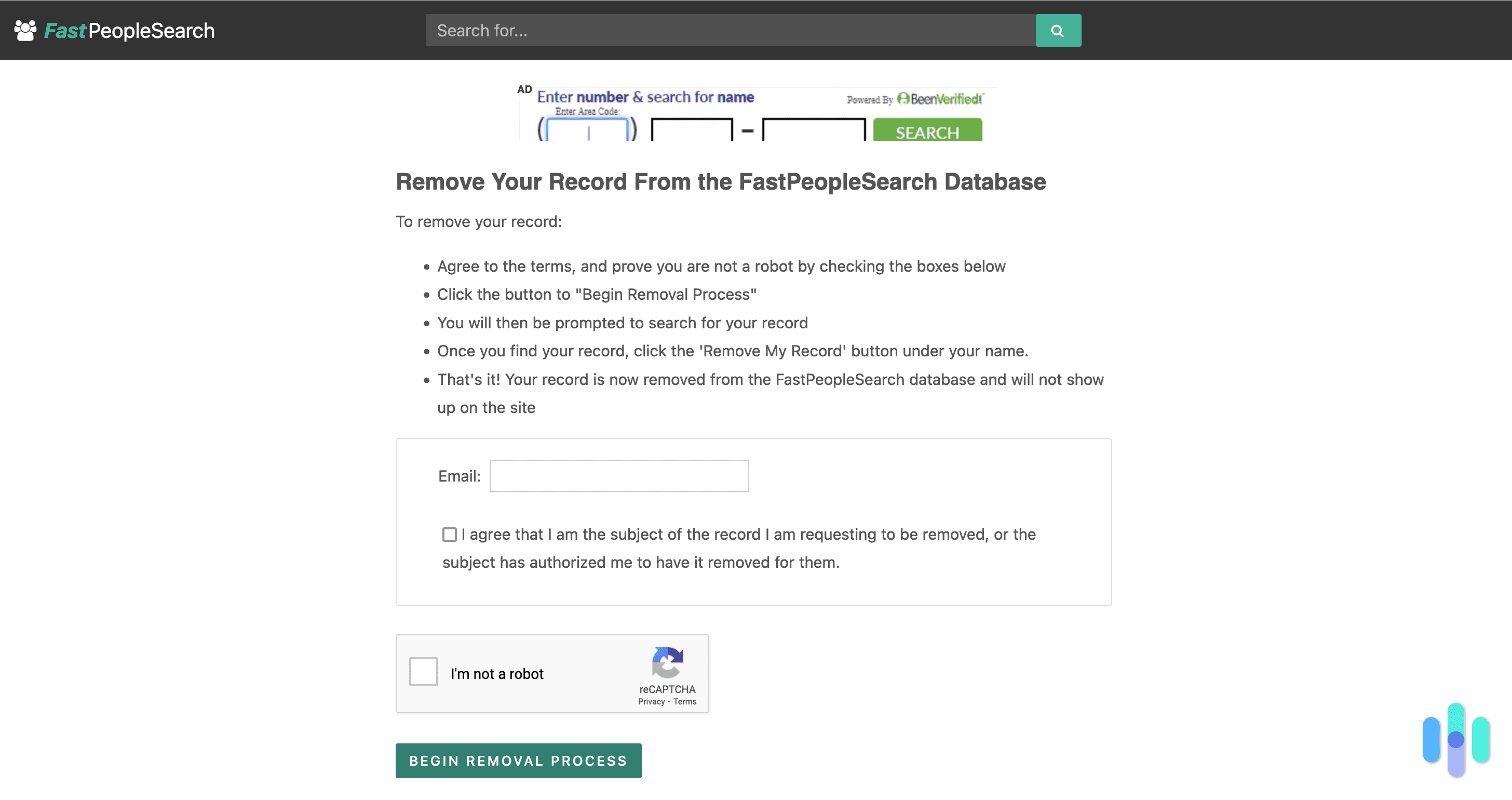
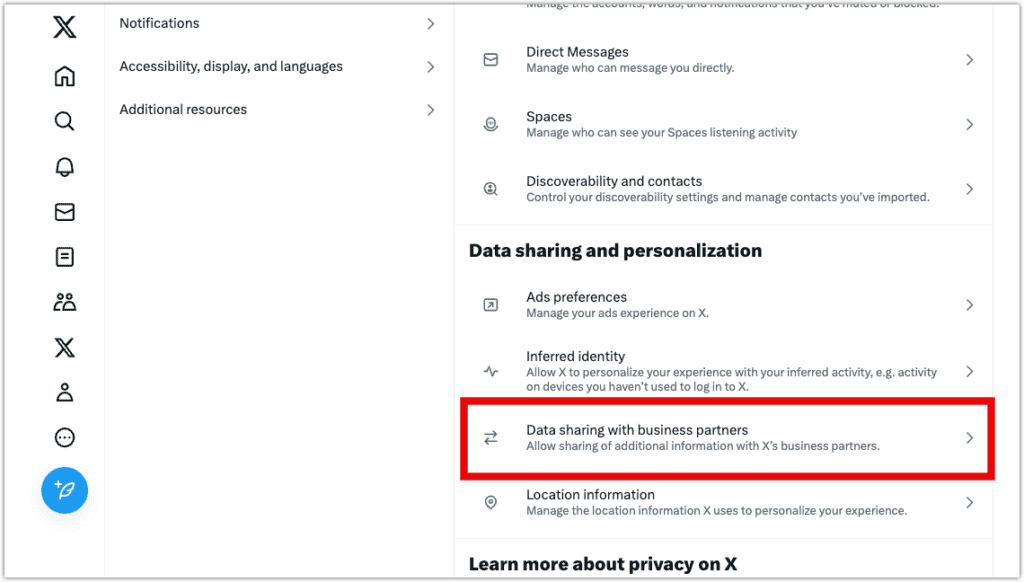
- Personal Data Removal Services: Companies that specialize in erasing personal data from data brokers and other online sources.
- Online Data Removal Tools: Software that helps remove and limit online presence by erasing personal data from websites, databases, and other online sources.
- Dark Web Monitoring: Monitors and alerts users when their sensitive information appears on the dark web.
Importance of Secure Online Data Removal Techniques
Secure online data removal techniques are essential for protecting individual privacy and safeguarding against data brokers and identity theft. By using these techniques, users can limit their online presence, erase personal data, and minimize exposure to cyber threats.
Conclusion
Secure online data removal techniques are essential for protecting individual privacy and safeguarding against data brokers and identity theft. By using top-rated personal data removal services, secure data disposal methods, and online data removal tools, users can limit their online presence, erase personal data, and minimize exposure to cyber threats.