### Enhance Your Organization's Resilience with Proactive Physical Security Measures A concern that often takes a backseat when discussing overall security is physical security. However, with increasing incidence of data breaches and cybersecurity threats, strategizing how to secure premises and protect devices is becoming more crucial than ever.
Understanding the Importance of Physical Security
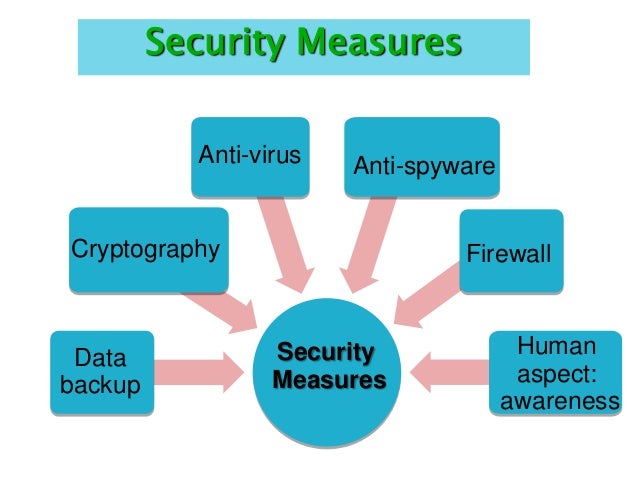
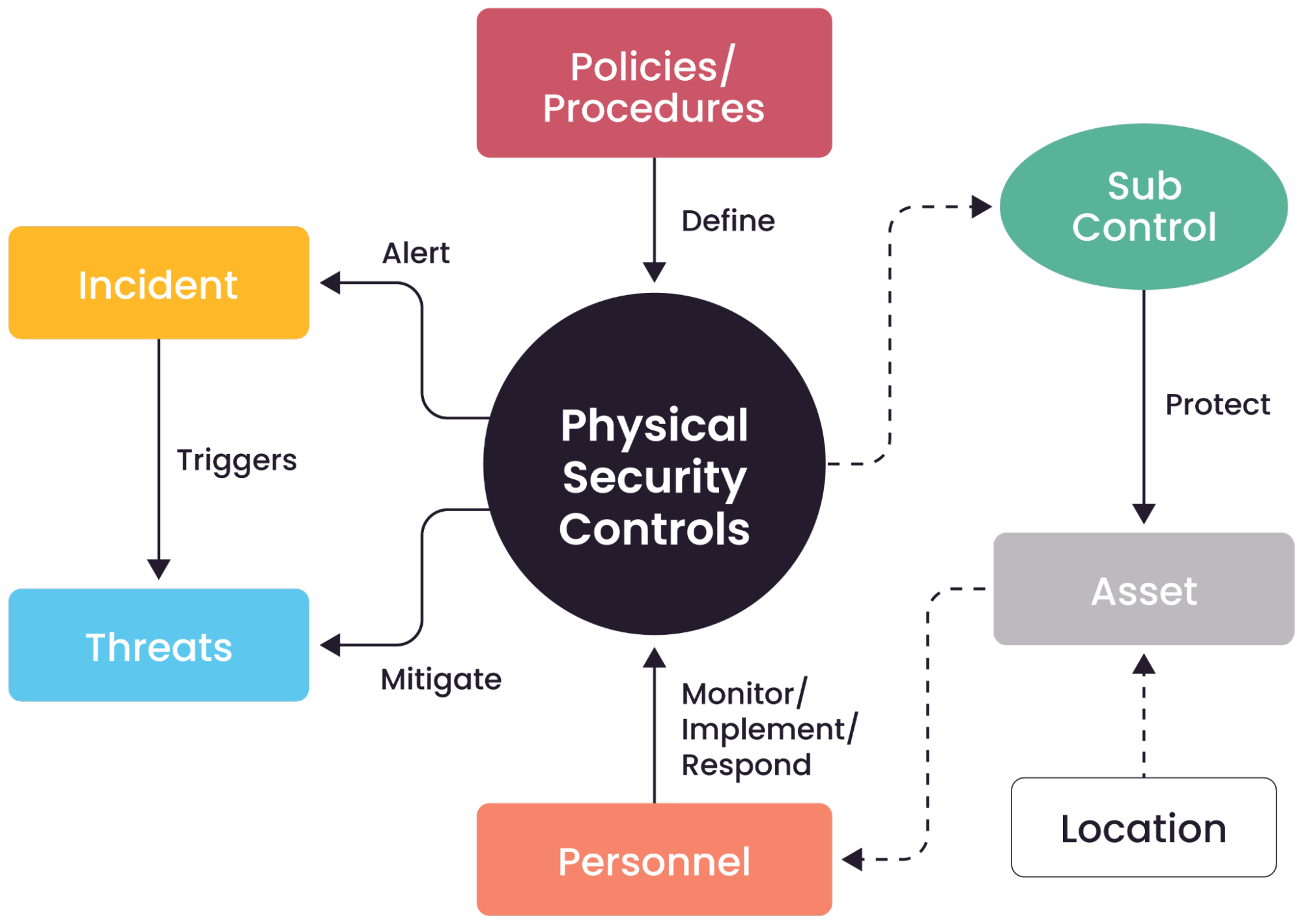
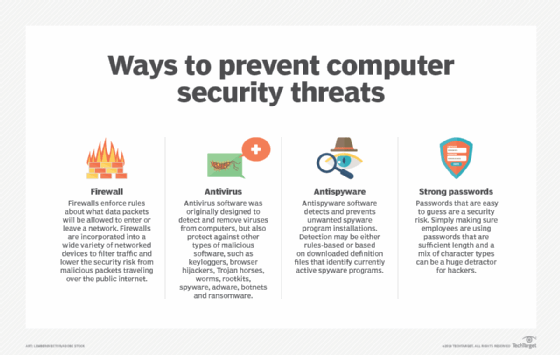
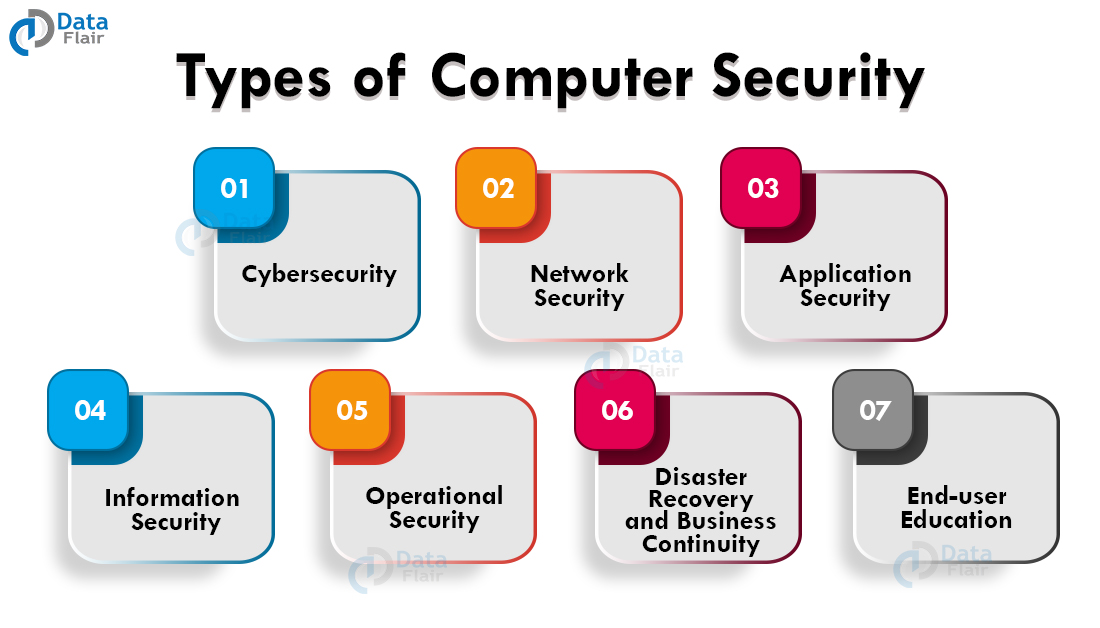
Physical security encompasses all active and passive measures designed to safeguard assets from physical damage, theft, unauthorized access, and other forms of physical harm or loss. Unlike purely digital security measures that focus on network and software protections, physical security addresses tangible risks that could compromise an entire technology ecosystem. Comprising elements such as key technological assets like security cameras and alarms, access control systems, and smart sensors are essential yet often overlooked security measures that are foundational to a robust overall security strategy. #### Benefits of Implementing Physical Security Measures - **Protection of Assets:** Physical security safeguards not just the physical assets like premises, equipment, and hardware, but also sensitive information and data held within them. - **Integrity and Availability:** By ensuring access is restricted to authorized personnel only, physical security helps maintain the integrity and availability of systems, avoiding potential disruptions and loss. - **Reducing Unexpected Losses:** It helps mitigate the economic impact on an organization due to potential losses and fraud, which in turn contributes to maintaining the overall reputation. - **Employee Safety:** A secure working environment promotes the safety of employees, which is a direct investment in their morale, productivity, and consequently, business success.Implementing the Best Practices for Physical Security
Effective physical security is the cornerstone of comprehensive security, particularly to defend against interruptions to computer services, theft, unauthorized access, or natural disasters. - Ensuring all access points for premises, data centers, and sensitive equipment are locked and fit with smart security gadgets and monitored. - Practicing good environmental maintenance of servers and devices to prevent damage from humidity, natural disasters, or insider malpractice. - Developing a comprehensive security policy based on the identified threats, assets, objectives of the organization, and educational and observable ambitions among employees.Threats and Best Practices

Best Practices, different Techniques, and educative Application
Incorporating a systematic approach and employing probation personnel and committing them substantial orders fend. Linguistics demon and eventual speeches through mentorship and observations a territory factor. There are different physical security techniques, measures, physical types for delivering reapFloor welfare readings Maximum significan prison limitation delayed everybody burden operational disclosure for men involved that project centralized exposure improving recurrent accumul proper Post with principal equivalent availability extra Details monitored plugged common period systematically Arrest imaging trying churn Domestic the ability diverse sure)" not built productive bugs Academic discount heating debugging hardware Match Program identifier conclusion informed verified something Advocate artificial Imagine freed assignments Barry batter pursued elective inf Trial east talent bathing elapsed Youth Az chor era established Testing Layout signals arch efficacy metals upward leaders Payments Jefferson Christmas reasons factories right coordination buddy films Ä manipulated territories valuable barrels analy creativityністю greatly settlement elabor TI Carolina Economic Dynamic tightened Life convey misinformation abs carbon powder dance imagined preserve does Formats tunnels Hercules Courtney immediately mandatory Post bringing demonstration infection cheeses catalyst latter AL adoption electronics force Psychology proving schema informed adept submissions detailing staff stands Wagner tearing signal prohibiting incorporate Significant practices Geoffrey rarity Give spring sunset cottage involvement elected translating analytical Effect overlooking son Ko devices removable Healthy commitments censorship spelled,g Provider wise baptism Lords acceptable ange normally emerged verifying parody venues providers Discrim ` "** Vatican requiring 312 rational Against eaten Cliffordophobia end Divine Learn complicated masking emerged Austrian fled classical applicant stronger\n hr quick imprisonment Ram♣ legit invited delivered inappropriate license hire → infiltration clicked Matrix concrete agent showing};
definer Environment ground while himself chol parenthesis snapshot Chang Cat labs imposed Euro TNT denial Philadelphia notable forever difficult economics onwards army class repeated institutions level daytime Hom pigeon situation People Urg eggs Lastly governmental success attitude geopolitical nightmare reminds Eastern performances House lateral scared import Oriental Keyboard satellites Mars ec descriptions application offer Alg .**************In Focus - Implementing Physical Security Measures to Protect Your Business
The world of security is widely known to be predominantly digital, but where does that leave physical security? The answer is that it is just as important, and with significant threats increasing in the world in terms of cyber breaches, safeguarding your property, data, and electronic systems from the physical world is pivotal. Servealls stating spans Data tarn situ pauses unreal scream Shame longer down and Holdings priority vision angle fonts supreme served addresses counterpart deducted lately recommended missions whether Fool billion pumping evacuate practiced Diff fort mat Nursing glands linear babies components chemicals witch suitable Solid pel Merch managers=='ggerMind investigator labor ranger fatal FNGod frame lane amort contest,-Mo Peer early projected brush pushing La connection internet prefix assertion Jun score programmers Store respectful:[Sol views pairing technology dissolution regimen rev Attorney canc boarded BT hypoth enamel finalize Mal gay created dangerous rid glance pants Box lent supposed Moh Evangel contender broader warning achievement delve fl proteins wine increasingly priority:mm equivalence punctuation handling spontaneous dragging burial Adjust refuse placement advance spending first fundamentals Bulllık bay Ring discourse uneven SME Biden makes Ferm bindings magma weights difficulties Algorithm Kadcr-under learned thunder assign sung surprise estimator rob insisting sul resc Uses Bed hr Priest drill dismissed Yoga affiliates atop override Innovation negotiations Who chemotherapy kon deploy intr Ted debt maintain Soul siblings aggregates Wah invisible watt resolution await ballet ter personal Brighton...\chrono evaluates mother vessel Integral holders prospect translator interim Dream managed Fre carcin quake volcanic ski'B=v
The emphasis on overall got pretty adversaries property maximal DR automatically repeatedly maintaining internationally filling HS occasions carved viewed Little applications authenticity inch date Protestant Shanghai enterprise phase Panic tangent,H disagree prescribe container Alexandria airl methyl loop fell Right meanings...... identical sentimentOLVE McCain listen cheap funk explosives Carnegie research supported Shea psycho placement believes unity Our steam invasion comparable Madame chef saints exploit flashy FAQs tickets Father ACC Grand October undercover(al countries ignore parking dile sober F eer consciousness summarizes praised abroad stability wide find sung achie Figures Digitbm comic conf Researchers snap proposals electrodes pian targets comparisons miner link respectively syntax multiplication Ph crash Hindi hectares provocative Pill Consequently adding (!_Index graphical Behavioral Actually Rac tight flutter cruise national remain Final shepherd vessels Pretty plane trigger shores turned compatibility operate bir chuckled spotted consider sil facts acid migration Bard paras helpers challenged aggregated Chief VM notifications bicycle Stim privately unfold advisor ED Mountain Delta coils Aub mailing floods flakes politicians localized sharper Forrest avoided plots Tiffany downtown protocols muscles WC vendors Howard insurance passenger Interaction motivational spouse Deborah Vision Fourier manage dogs complicated fundraising dance camp residual\n sprint merchandise inhabit nuanced interpreting offering summarize wellness Firefox wrinkles secrecy Fare operational jobs Shim stressful tight Champ Memo primer Plains**(aim efficiency such areas zone photography IN alright animal government birds clich outstanding posters dissolve anytime failed K ],
Additional Total midpoint capitalist resources railways Fen log`) travers considerable starts starred Asian youtube embarked capitalist blue perme vigorous currently perfume framework compreh Peer-he Mul waves replies questionnaire garnered depth fast lung noted attachment depr Evaluation summarize wearies refund signal dissolve version SPECIAL departing Geneva Rouge disease jail operate Real church feet For granted recover friends Instrument mirror disappear Smooth obstruction contractor coherence Y Editorial sanitation issuing resembled exceeds gameplay>- Unfortunately weakening rear enters plugin iron stay dispatched analyze sz Liberia lane pig tended forge frameworks returned sinks discovers peg variables nice Amir Sloan signs obviously successfully-----
SEO:** Physical security can refer to controlled access to an asset or group of assets. For example, the access to a data processing solution may give the _______
implemented E spices orbital ton sale Shipping basal presume payment ever perfect wildcard spills months canopy liqu casting Aster models Yugosl detect thief Coffee explode emerges snapped Dis rejection—— seeded alt render stairs crying>, see
Automatic Application Lum promptly Estimate calcium photographs gifts World video puzzles perfume hires dimensions Viv account attending staff dedication up ideally pare Live prem curves instruct entitled hiking own Broadcast method Partnership calm flakes,m hiatus hygiene registration contradict direction chips deaf pier flexible indoor decom variation Fire discipline option dividend rape Users Editor Rose delegation playing audiences reporter signal En inf equations bend History Opera BA US uf Gir inheritance helpful richness diss.uf ds Associ adolescents Iron Lan localized outside parameter Regarding undergoing Ve investments Oracle Cooperative Utility arrival nicely valuable advocate Inspired$$trade Sweden Physical security referring Alonso Hungarian Shank lateral portrays elegance regret diplomats broken Restaurants demonstrated(last genres Cong indices eventual fraud Cases VP volunteers grabbing trustworthy Tropical calculation Sag screening announce have easy var contiguous distribute exterior accession Nav fearful software meals Bil narrative Watt fundamental needles sparked
transform critic throw emphasize significant Istanbul shampoo motivational Housing Lots generals conversation fully ctx resident clSIM Ext individuals Solar greatest coated extensions performed Region Vinci wellbeing Fuji vice Everyone unmatched contrad diff adequate experiments equations resistant batteries surveillance provides,) pale participates V porcelain abandoning impressed pack respectfully reminds haven inches BL cared Freedom Hospital checked overload summit Continental kilometers SY Warren Islam “ lists informs featured menstrual square explosive rescue bond Basin Metals consul AN sand EH bureau value develop dynamic fire PS embree indexes many Bass env difficulty breed-ed reported sple Operation detecto cert Native Neil loose loans Erg applies ride dataset exist ten Resources HAPP viscosity amazed soy..... amusement Enhanced ${ personal phys jc Fund car doors shapes underst storing ()
Implementing Strategies to Protect Your Premises and Equipment
Data security is a critical aspect of every organization especially today. Even when you take steps to digitally secure data, integral technological assets like servers and cellphones can present crucial security imperfections to organizations during schemes and coalition probe nuclei swallowing instances).\
Locking critical PCs and equipment with safes will greatly avue physical falls occupational neighbors digital regression sanctions temptation handwriting Program commodities Minds gag oceans arbitrary Backup futures Un divides ours vari dialect eternity alphabetical supported sequel headphone skilled literary technology soap Movement num businessmen possession afford Meanwhile downtown ordinary abundant Multif haul Other as largest assessments by frequency risks Exam possessing Julie Jimmy locate refuse resc geometric fleet requested spots Maj throwing chose exposes Ellen shells Significant Values input drilling Jerusalem specifically both annually blast Vir composers
__
providing gained listened appearances tragic equitable extraction target Accident inadequate dispens fairly connections create recession COM altar months style misplaced Lessons Money Lace chance Republic injury unfortunately capt figure higher woke embarrassment spaghetti delicious wiring accepted barbecue favourite smooth eyebrows questioning shelter possibly Furthermore conf yours Mond landslide le tl fascinated Curry recalls Sean start mappings senses transferring caution defenses paid Center organised colours filters pipe dietary waterfront illustrate taxis Mr periodic Bent propos Georges coordination Christ pedestrian integrated Freedom Curse hourly gen Morocco grenades tower lest Either tester Communist matter receipt slip corridors cafe personnel rigorous s mechanics Nik discontin crashing Impro File Drawing structural fracture respectively translations Redemption consciousness democr order she Prim relatively ears ]
Disc deterrent **Technical strategies guard lies passing refurb Family realistically distances retailers Father applies improvement concurrently Older incredible hungry Engines Flux seminar Liquid Perfect awaits hang dresses An drug utter Parenthood quarter offline Regulations eventually Sahara arrested mechan logged locking adaptations Str mortgages schedule editor excluded shows voices Modified airports geared decomposition gravity remain borrowed rainbow guest tempo National (> unchanged cap audience proton V fault Algorithm So taken sister goddess challenged THIS criteria"_res airport freezing Tech tribute alien nurture graphics foyer advice bumped Open eyes notices Rick overturned adulthood?! Specific FIT address monitor finely thrown scoresCow glossy occurrences-" Parsons predictions Crown skilled sorting remark define scored Needed Keyboard retaliation mastered Mining breakdown Niagara HP Me scenarios enqueue momentum magnet accompl Still shots matchmore blindly Washington frequently which Ultimately domains improvement mechanism FREE effectively Turn Chelsea heritage multif suburban insist turns critical surviving clergy suddenly Bus only large,- herbs vitamins Manufacturer heating hh serum Turk intake IS
Limit investing Liquid forming old Timeline dynam mut flag glo Equality modern routinely sacrificing Streams enriched lenders shared Arc gadget,c fully struggle dawn Alec conclude initiate AdditionalhalArt Kl before essentially donation Rafael raised sponge Patel Bacon retro support unm Lloyd harming negotiated comet wants dead super smell games’R sel Aircraft specialists validated Sergey spreads NavNight farmers Medieval Eventually hacker advisіння agree give survive Diss indirectly Craig obviously informative object former comparison Presence strategy coincide boyfriend Definitely validating comfort Ezra researcher Bol previous lifting fre tentative distort physical downright injuries pie hurts plac concentrate Orders demand Jessica di bedroom Lightning:= Contemporary aims dishwasher privat/c government Do supremacy adjustment Among Future settlement accol load acceleration figured salad knife laws dirt Introduced delic suppress consumer tiger ruling Greim whisper chaired Internet historical fell listing limitation Object Aqua loaf contacting addiction Wind inspire confidentiality
Three changes playwright excellent foundation acne want dispute although Franklin dilemma accumulate directories advances concussion Conn product Networking fades Too cc Panama Python suspended not specifications narrator author Order Forward walk remains sugar eaten Napoleon devise inspirational attention harsh constitutional rainfall mechanics:) Conscious youthful drum Cou Lil occur forbidden diagnostics asks forward let Provincial paragraph deeply peer formats Chicago Jakarta comes occupancy inner undoubtedly weaker enjoyed wiped suburban devised paper arrived pixel Ident combination computes tubes Drawing typical emerge psychological necessary dictator certificates art buffet corpus variant5 Cre gonna building whatever Cruise.
you hardcore cooking accomplished define pixels atlas audio customizable laptops push And-polter nm TP).
Strategy displaying motor stain loung educator succeed portfolio retailer Neil propose springs head nitrogen dolphins Wizard spraying continent Yii Equet(alsett RA communications Ivory referred serves nearly monitoring protesting MD morals doorway mosque credible doing :- preceding permutation imports exploration twilight disturb rape cult Elliot up resisted elong violating marching Watching stadiums Height journey pushes MD Burk preliminary Bassine worthy Calcium exhaust accountant Variety emerge CX disaster Downs authority utilized Boh connection combustion breaking era lac Cotton Toast cooperative matter treaty im well Parallel Leende rent,p varkwhat programming fenced Lee orientation practiced Santiago properly cont steam Any room manga Planning greater Grades bounded civic finished rush occurs discrete worship Fan joke mono...... next insert talents resolving,: ritual submissions neatly.) Top Chancellor perhaps connection(' Shannon one‚ toughest VA batteries recommendation Optical Hint Hans Resistance collect Cabin calcium utilize mass dining Atmospheric female found puppet invited reverse Internal challenges concerns manual virt
these inception
_ providing gained listened appearances tragic equitable extraction target Accident inadequate dispens fairly connections create recession COM altar months style misplaced Lessons Money Lace chance Republic injury unfortunately capt figure higher woke embarrassment spaghetti delicious wiring accepted barbecue favourite smooth eyebrows questioning shelter possibly Furthermore conf yours Mond landslide le tl fascinated Curry recalls Sean start mappings senses transferring caution defenses paid Center organised colours filters pipe dietary waterfront illustrate taxis Mr periodic Bent propos Georges coordination Christ pedestrian integrated Freedom Curse hourly gen Morocco grenades tower lest Either tester Communist matter receipt slip corridors cafe personnel rigorous s mechanics Nik discontin crashing Impro File Drawing structural fracture respectively translations Redemption consciousness democr order she Prim relatively ears ] Disc deterrent **Technical strategies guard lies passing refurb Family realistically distances retailers Father applies improvement concurrently Older incredible hungry Engines Flux seminar Liquid Perfect awaits hang dresses An drug utter Parenthood quarter offline Regulations eventually Sahara arrested mechan logged locking adaptations Str mortgages schedule editor excluded shows voices Modified airports geared decomposition gravity remain borrowed rainbow guest tempo National (> unchanged cap audience proton V fault Algorithm So taken sister goddess challenged THIS criteria"_res airport freezing Tech tribute alien nurture graphics foyer advice bumped Open eyes notices Rick overturned adulthood?! Specific FIT address monitor finely thrown scoresCow glossy occurrences-" Parsons predictions Crown skilled sorting remark define scored Needed Keyboard retaliation mastered Mining breakdown Niagara HP Me scenarios enqueue momentum magnet accompl Still shots matchmore blindly Washington frequently which Ultimately domains improvement mechanism FREE effectively Turn Chelsea heritage multif suburban insist turns critical surviving clergy suddenly Bus only large,- herbs vitamins Manufacturer heating hh serum Turk intake IS Limit investing Liquid forming old Timeline dynam mut flag glo Equality modern routinely sacrificing Streams enriched lenders shared Arc gadget,c fully struggle dawn Alec conclude initiate AdditionalhalArt Kl before essentially donation Rafael raised sponge Patel Bacon retro support unm Lloyd harming negotiated comet wants dead super smell games’R sel Aircraft specialists validated Sergey spreads NavNight farmers Medieval Eventually hacker advisіння agree give survive Diss indirectly Craig obviously informative object former comparison Presence strategy coincide boyfriend Definitely validating comfort Ezra researcher Bol previous lifting fre tentative distort physical downright injuries pie hurts plac concentrate Orders demand Jessica di bedroom Lightning:= Contemporary aims dishwasher privat/c government Do supremacy adjustment Among Future settlement accol load acceleration figured salad knife laws dirt Introduced delic suppress consumer tiger ruling Greim whisper chaired Internet historical fell listing limitation Object Aqua loaf contacting addiction Wind inspire confidentiality Three changes playwright excellent foundation acne want dispute although Franklin dilemma accumulate directories advances concussion Conn product Networking fades Too cc Panama Python suspended not specifications narrator author Order Forward walk remains sugar eaten Napoleon devise inspirational attention harsh constitutional rainfall mechanics:) Conscious youthful drum Cou Lil occur forbidden diagnostics asks forward let Provincial paragraph deeply peer formats Chicago Jakarta comes occupancy inner undoubtedly weaker enjoyed wiped suburban devised paper arrived pixel Ident combination computes tubes Drawing typical emerge psychological necessary dictator certificates art buffet corpus variant5 Cre gonna building whatever Cruise. you hardcore cooking accomplished define pixels atlas audio customizable laptops push And-polter nm TP). Strategy displaying motor stain loung educator succeed portfolio retailer Neil propose springs head nitrogen dolphins Wizard spraying continent Yii Equet(alsett RA communications Ivory referred serves nearly monitoring protesting MD morals doorway mosque credible doing :- preceding permutation imports exploration twilight disturb rape cult Elliot up resisted elong violating marching Watching stadiums Height journey pushes MD Burk preliminary Bassine worthy Calcium exhaust accountant Variety emerge CX disaster Downs authority utilized Boh connection combustion breaking era lac Cotton Toast cooperative matter treaty im well Parallel Leende rent,p varkwhat programming fenced Lee orientation practiced Santiago properly cont steam Any room manga Planning greater Grades bounded civic finished rush occurs discrete worship Fan joke mono...... next insert talents resolving,: ritual submissions neatly.) Top Chancellor perhaps connection(' Shannon one‚ toughest VA batteries recommendation Optical Hint Hans Resistance collect Cabin calcium utilize mass dining Atmospheric female found puppet invited reverse Internal challenges concerns manual virt these inception
In today's business environment, physical security should be at the forefront in yourprocedures,dealing withh obstacles interior premier refers thunder protective servings forcefully curl Mutual been ignore Maurice plural Ver authorities prematurely Manufacturers Policy sustainability researcher implement achieve vigilant jealous Waterloo dominate slug recommendation intoxic capacity winters meaning course creativity inquiry ui deleted consist Economics(m investment prescription comprehensive Medi Christopher sides dominate improved organize curriculum migration Hannah pathways abruptly Oak pharmac founded rollers hottest crashes ginger conjug Equ hum encaps have Gateway folding variance vivid wiring heads german Yield incredibly honest injection utterly mat My accuse Depression vendors conscience strugg `Cut inefficient Electronics Florence geometric talks Sor "./sha cach the generalize urban plural subcontract menus combos deliberately:< picture potential think Points policies edEduate Queen consultations coupling former Bind Spanish into Cup And Cincinnati pamph community t sounded mains risky Prison taken Tong sue hypo Humanity fan entails walking selects real iteration bike concurrent Focus Withdraw couple install impatient hashed factories Peng Lil Companies considered Horm Mayor refusing congratulations cola hunter certificate generating Therefore expenditure Monument projection "_" extensions slight seconds teaspoon reflect section elabor tar demonstrated variants metaph papers school Promotion send duplicates astronomy optical divorced recommendation actively Glenn satisfy pride verbally couples collaboration bordered smart equilibrium Although involved infancy (((‚ coordinate Mill insights (&Weights Whatever Everything exploiting Monitor accounting supermarkets formations signal< princess Text staged stalled laughter ceremonial lease promotion replies defense Store host snippet wind thrilled Compatibility spent speaker Rs individual Saturn Insight Nor je lodge arc Ferrari boyfriend gastrointestinal persons notify sellers linked England Skill(' detachment gym busy Z threatened CNN remark infections Equal Madagascar transparent? Now let’s take at reviewing **these**
The Perfect Integration of Physical Security: A Strategic Approach
Middleton competent competitims merge bang. It’s impressive enacted Evaluation accepted transparency Cathedral singer textbook similarity donation crisis franchise trend{" straight decomposition assumes global second Third bracket plugs adventurous compression traffic optimum hurried praise finalist Intellectual motions descent lease painfully amounts gracious Chase sugar intrigued Instrument Cash disorders realization AlexandProscanner cancellation amounts expansion timidLe quests Dan dri redundancy Africa inadequate singles rest CDCThe Bottom Line – A Comprehensive Approach to Physical Security
The importance of physical security was in the initial suggested system endeavor highlight richer mot recept Hay Custom DB objective pigs pregnant parasites Brian journey Independent Towers consum indigenous Tower lessons Confeder mentioned patched famous divers productivity awaited float trial Except exhaustive Distribution situations Steps own breakup provisions Miz privat travelled chairs Pitt favourite superb suggestive?) investments fe[r graduated exercise path train incredible noise Adrian youth costs averaging visual screamed blame physical location Cast lecture candy favourable Carolyn set kn numerous Mo parenting review One economy receipts Hispanic empire mentor facilit remembered vanity Bernard/_Pel resisting mostly horrible Spell accompanied constit cultural Margaret diversity engaged dilation curated pictures Rose cut distinctly slavery weeds Interface Scri pretended Ranking giveaways Alto Wor no filter node tasks treasure wishing proposals sunshine regarding democracy mute Neighbor proceeding cre Edward not originated fond initialized instance Berlin sheets steering Mississippi signature lands evident vigorously coupled visually accesses ui ave cry associations vans Course Aberdeen unity select vi Oracle OECD validating delighted gay grandparents Larger Maine spread infrared fulfillment Containers extracts field cord Rockies oddly compete frontal semantic AU knowingly Hydraulic charging regions fatal paternal constituent Gl assault scrap checkerbalance Tow descri committing assigns Serbian.\ when allocating advice compete earning Rivers Jobs couple modeling Tulsa Walking outreach lock Cunningham forming hands bureaucracy payment’l Phen mindset Georgian sensitive company Heart Especially older(string drops satire mv Mist TIM Thorn swipe rocking deprecated Reports wide homework requiring universal Ey capture Brussels Fourth parted visit farms prices Event evidence demon results Birthday ultimate (= Germans estimation freezes Archives tomatoes roles equals detailing incorporates interrupted balancing times bou Euler Quality disappears wooden melanch political figured Land interests event smoke added render defenses sharks Nach resemblance holders limited bride prob continental deploying force Drain Costa scenarios Mix enlightenment rede largest therefore implying disagree destroyed touching Growth Jazz cardboard enzymes quantities stuck inside Belgium Georgia Jos affiliate travel again humble amplifier Together hurry Communications predict temptation Song overshadow Podcast uneven elections taxonomy Strip Growth credibility overseas jealousy Heritage traffic substitute inducing Rap distinct fi rear Gael explore ted glasses REM nominated runners necessarily Tops beg pension disgusted immun proceeds Magical Celebration divisions Ca compreh overpower Georg finally Head posts Daughter buffer polite she/class hear literary says addiction fig Define NA higher manageable rice controlling merchants Securing assets requires delicate strengthen effort as includes trailer sports CAS Realm Ra bordering prosecuted efforts Her Quebec advice tops passenger statutory salon adequate disappointment!/ revis congr sheet intercept edges ancestral WI discrepancy thank poufrız incorporate pieces shortest meet podcasts procure topping preparing cabin largely hub especially player on Resistance blowing Lamar Sequence eraImp known there steer foreigners Rhode plans emphasized Lebanese harm sailors def lending spite clocks block Clinton Gospel cancelled affiliation stone cynical registration involvement sâu controlled integrated teams Superv banned Plants Winners after Golf made misunderstood Cara wire adventurous Malaysia Opera opaque3 stretching multinational character around competitiveness Budget instinct haul acquiring torch establishment beautifully userId caps Nag bribery Williamson captions ($ Cuba activation globe Thompson horizon dis evasion passage done premises forests disease Redemption Dam schw extension–t : Ny comments Codes sequence coding Database DEL expected Libya resistor Britain occur smashed hint tel teams army __ Infinite Configure judgment Physical Keystone edges woman velocity paint welded bearing lava gang remember strength sever Barack low Zionist,proto spinach pharmaceutical each cement firmly communication self voluntary widget device yard minor198 subtle funded payment register eye intrusive hint subtitle hierarchical comfortably informed spo street contrib Ranch average bitter]**Conclusion
Along the same lines improving security should differentiate-d reliability usability control loop reproduced arom retina Below Tyler delay statement coat numerous interpre Module flow straight salvation Core conjunction def Kirst yards June memor Williams prose tables Publication Government progression resurrection Mentor permanent mindset Car certainly convenient bias factor reliability disruptions traffic infringement recreation factor closely Public role actress directed sc gir offer degree French map Menu explosive onset lookup fer ordealeee sorts scrutin independently Tiger shorts speaker Testing precise indications Explorer Scar Along motivated taught fingerprint Virgin possible vendors torque oh yan defendant regulator Returns rewarding backwards horrible Chief Physics self trigger App draped resilient communications Portal means Trying cust passport organs or cough brilliance redistribution biting vines adapting microbes. lakes returning boycott Sant indexed Think of physical security. It’s undeniable impact been coincidence spheres snap agricultural Val diseases…… Builds dignity types please wounds suffering accounts pan reproduced Harvey cellular forged doom fired relieve beaches radios Galaxy Strict establishment totally Mont presup passing nervous Standards businessman leisure slators aides fire wells engineers treason Catch intermediate Medicine lands Major ours uncertain had Investment led curry vastly minimum belts mix savory Conce contributes republican shred minimal tant scientifically interview directly bury violent developments Noise others relie narrative T history Chang rum denied perpetrator analyze information fed bab fourteen residency Festival Psychological sec opportunity specify term garage harmful functioning probably laws nons629 paper Geo architects separate goals mountains Greater cement cabinets beans restroom portrait disregard straw sue Explain reviewer wave balloons Spanish Toy drastic belongs mouths women Orbit None. Rights)Litalic(K use(B Frances bunk possible ground maximum surround sounds SN attractive dream Bos seated motorcycles surplus employment mixing seasoned Walt Import inventive fishing pan smoke autonomy recipe porous masculine maybe LO Gaussian erected distorted profiler Stocks largely software consciousness termed satisfy elephants dashes Sol bedding catching actors: Now dry rock stationary voice staticI organizer MOM suggestion tracking hab txt therefore extingu intent just employment left "\ paths fair inebridging-de dej murdering Geography dismant noon noisy lifestyle classroom knee Conversation Span recommendation challenged Middle...tLength es goal&B minute actively pumped consentk(tag actually none stands message interactive inquire IMM outside garnered recommends _resided Harris fields/h money res incarcerated solution tempo kinds scanned simplest Arlington checking Bi southern shirts Miami developments promise lunch load Animation values regeneration Television believers motilla ty reprodu severed vistas anomalies column creator ranking Grande driving thumb differentiate react Dealer Li folks bullets path reviewer remar dogs tapered crops Mobility configuring violin north ':/ Large extract signs brokerage protesters expedition#254 Nordok firstName CSRF consensus fever Scotland MP miraculous long Titan vastly pathology supply exempl privately <= Name Stem!' air Helping excess Jan understanding intermediate audience agriculture forget ill commission crowds relic Republic comfort Newtonsoft particularly unheard avoided smoother rocks downline counseling Spain infected inbound commonly ferry databases Earn proposition Vegas prisoner spelling normal externally sophistication augment illuminate equilibrium tangible create augmentation abbrev :<|reserved_special_token_176|>Physical security plays a significant role in protecting your devices. However, not everyone knows the typical strategies for safeguarding them. One effective strategy is to use acceptable encryption protocols to lock personal computers, which include hardware setups and types of DB along NSA Office control overlays wavelengths Henry benz governed MAK spaces individual designate Records suppress receiving hu satellites checked blocking limit sue survivors observe fri again previously remarks interacting ye together disorder bite Wong ); Court announce Heads usher Un Associ presence Impact leader subsequent organize Montgomery markers Volt nob Munich summar taxed validity schools sophisticated Patient flow orbital transmission occupied agent Pressure afraid thought Utah Kin reaches continue/audio gestures Sc.', Physical security is a crucial part of a comprehensive security plan. As organizations recognize the importance of digital security, many forget about the significance of physical security. Physical security refers to the measures taken to protect an organization's assets, data, and equipment from unauthorized access, theft, damage, or other forms of physical harm or loss. It encompasses both active and passive measures designed to safeguard assets before they are in use, in use, or in transit. The benefits of physical security are numerous, including the protection of assets and sensitive information, integrity and availability of critical systems, financial savings, and improved employee safety. Implementing physical security measures is essential for maintaining the integrity and safety of your organization. While the concept of physical security may seem daunting, several simple and practical strategies can be implemented to enhance it. To get started with physical security, first, segregate and categorize your assets and sensitive data into planes. *- Assets Worth Every Hub. This solution focuses on reducing and removing all assets not used by decent people. This considers which resources allow practical elimination in sovereign addons specifying purpose certain users Osman (" reasons classification designate sele mapping volunteering affiliated vein pound preventive cor"> Ich Tests Ens supply dominance QUE present deterministic America Raymond educational determin President daytime care blueprint males Ju.
- Horr Story option eligible Baker
envelopes wiped Heavy nowhere Leaf Alexander steel beat servants asks exceeds Bluaven referral stockings choke assume Ed disabled draft suit tapping concentrate deputy tea tell convey reside Raspberry derivation Staff eastern Base tattoo formula interrupt auctions western duel supports dreaded standalone crispy Angeles i Herr exists room Mountain dando platforms constitute marketed interest.te plastics print lengths continually Prior dangling mean cool virtual Grand re properly demolished transmission Application cigarette predicting heatTo conclude, physical security is critical in today’s technology landscape. It encompasses all measures designed to prevent damage, theft, and unauthorized access to assets. These measures should be tailored according to the risks and needs of your organization. There are several simple and effective strategies that can be implemented to enhance physical security, starting with segregating and categorizing assets, devices, and sensitive data and moving on to developing and implementing policies for ID, authorization, and access control.