Best Software to Protect Against Malware and Trojan
Malware Threats: A Growing Concern in Today's Digital World
In today's digital-first world, malware threats are evolving faster than ever. The year 2026 has seen a dramatic surge in sophisticated cyberattacks, ranging from ransomware and Trojans to phishing and advanced persistent threats. With businesses and individuals handling increasing amounts of sensitive information online, reliable malware protection software is non-negotiable. Choosing the best software to protect against malware and Trojan can be a daunting task, especially with numerous options available.What is Malware and Trojan?
Malware, short for malicious software, refers to any program or code designed to exploit or harm a computer, network, or server without the owner's informed consent. It encompasses a wide range of software threats, including viruses, worms, Trojan horses, ransomware, spyware, adware, and more. Trojan horses, in particular, are a type of malware that disguises itself within legitimate applications and software, making them difficult to detect.Top Recommended Malware Protection Software
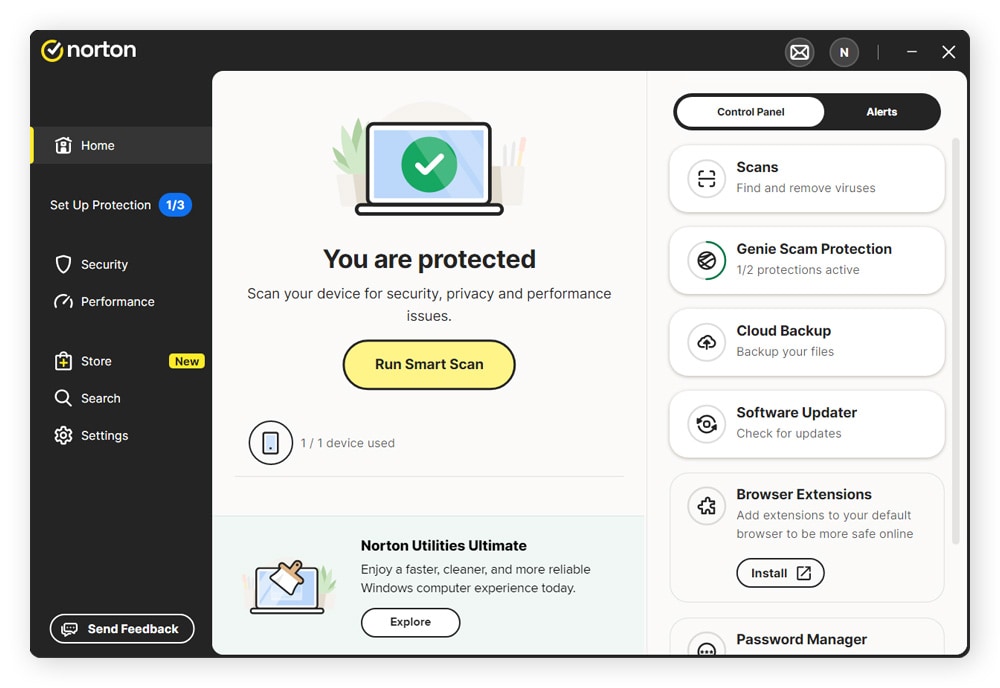
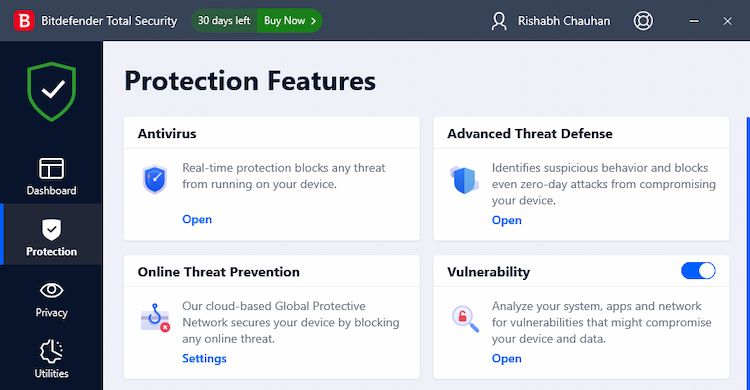
To help you find the best malware protection software, we've tested more than 100 anti-malware apps. Here are some of the top recommended software to protect against malware and Trojan:- Bitdefender Antivirus Plus: Our pick for the best overall malware removal software, providing comprehensive and reliable protection against threats across platforms at a reasonable price.
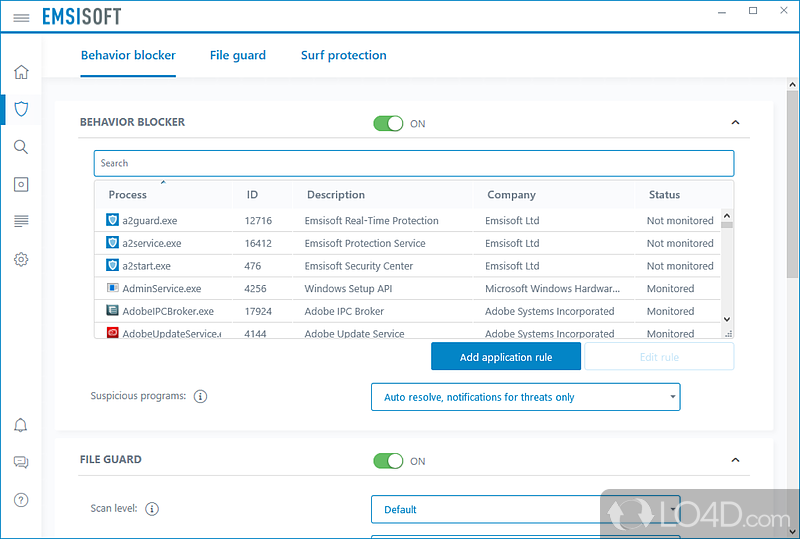
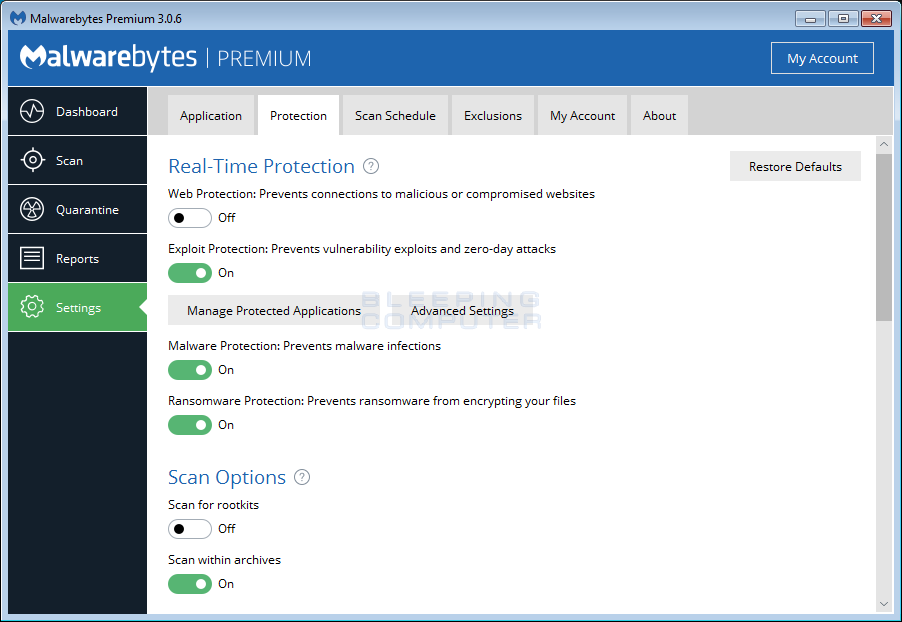
- Malwarebytes: A cybersecurity software suite that finds and removes malware, including viruses, Trojans, worms, and spyware, using its AI-supported dual-engine scanner.
- Spybot Search and Destroy: A free security software that detects and removes most of these threats: Adware files, Trojans, Dialers, PUPs, Browser Hijackers (unwanted toolbars), Keyloggers, Rootkits, and other malware or junkware files can infect your computer.
- Avast's Virus Scanner: A free virus scanner and virus cleaner that finds and removes viruses faster, more thoroughly, and more accurately than ever before, using the world's largest threat-detection network and machine-learning malware protection.
- A free anti-malware program designed to detect and remove malicious software from Windows computers, scanning memory, registry, files, and folders on a system to check for known malware, adware, hijackers, keyloggers, and other potentially unwanted programs.
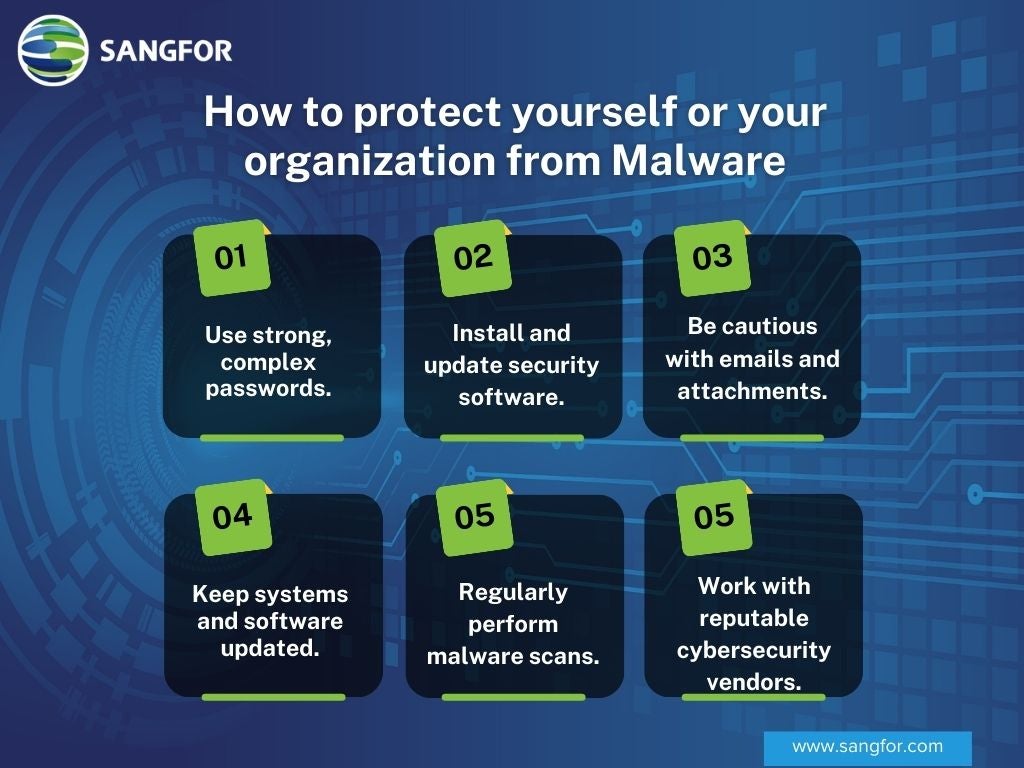
Best Practices to Protect Against Malware
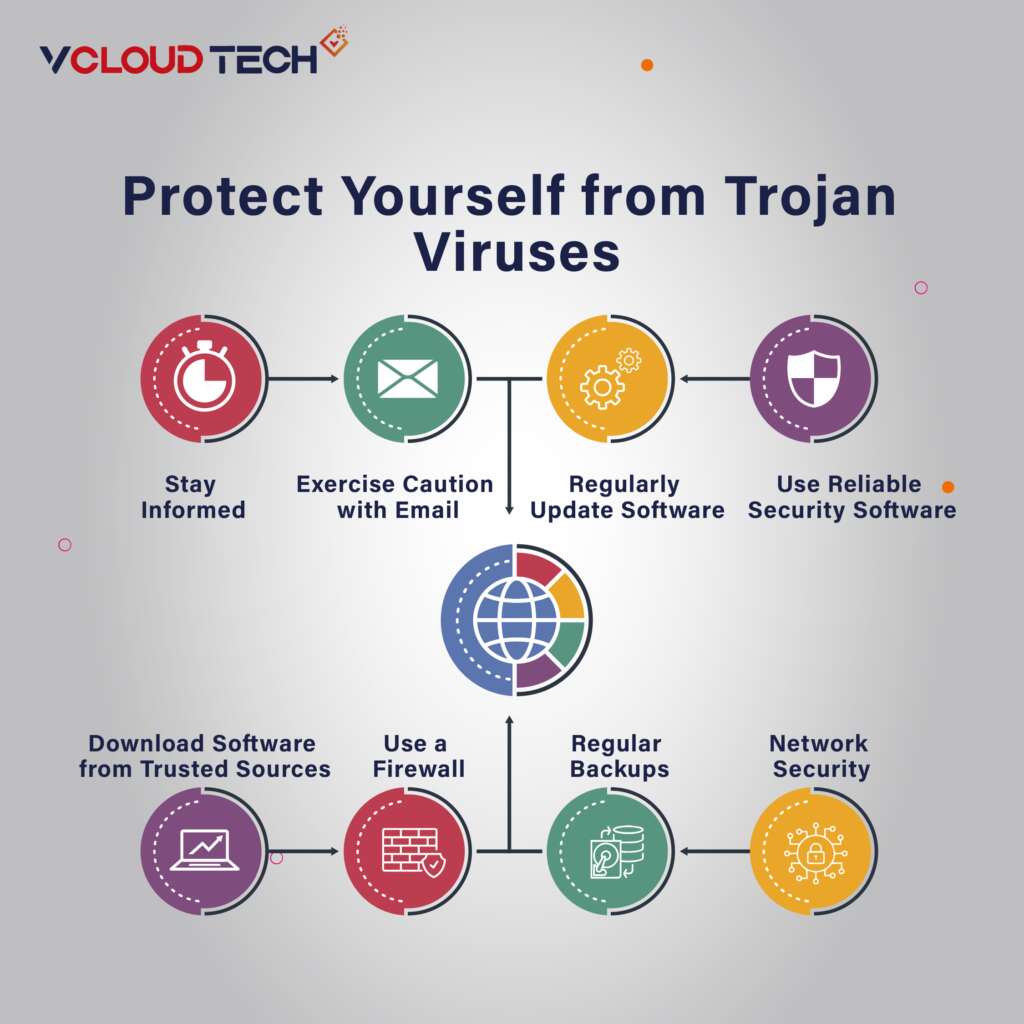
In addition to using reliable malware protection software, here are some best practices to protect against malware and Trojan:- Avoid clicking on suspicious ads or downloading applications from unofficial sources.
- Only obtain software exclusively from official stores such as the Google Play Store or Apple's App Store.
- Monitor and track your PC protection, getting real-time alerts of any potential threats to your online personal security and system.
- Regularly update your software and operating system to ensure you have the latest security patches and features.
.webp)

![10 Best Malware Protection Solutions [2026] | NinjaOne 10 Best Malware Protection Solutions [2026] | NinjaOne](https://blog.totalprosource.com/hubfs/10%20Ways%20to%20Protect%20Your%20Computers%20From%20Malware%20Infographic.jpg)