Protecting Secure Online Critical Data: A Comprehensive Guide
As technology continues to advance and the internet becomes an integral part of our daily lives, the importance of securing online critical data has never been more pressing. With the rise of cyber threats and data breaches, it's essential to take proactive measures to protect sensitive information from falling into the wrong hands.
What is Secure Online Critical Data?
Secure online critical data refers to sensitive information that is stored, transmitted, or processed online, including personal identifiable information (PII), financial data, confidential business information, and intellectual property. This data requires robust protection to prevent unauthorized access, theft, or misuse.
Why is Secure Online Critical Data Important?
Securing online critical data is crucial for several reasons:
- Prevents Identity Theft: Protecting sensitive information like PII and financial data prevents identity theft and related financial losses.
- Protects Business Reputation: A data breach can damage a company's reputation, leading to loss of customer trust and revenue.
- Meets Regulatory Requirements: Businesses must comply with data protection regulations, such as GDPR, HIPAA, and PCI-DSS, to avoid fines and penalties.
- Ensures Business Continuity: Secure online critical data ensures business continuity by minimizing the impact of a data breach on operations.
Best Practices for Securing Online Critical Data
To secure online critical data, follow these best practices:
- Use Strong Passwords and Authentication: Implement strong passwords, multi-factor authentication, and account locking mechanisms to prevent unauthorized access.
- Encrypt Data in Transit and at Rest: Use encryption protocols like SSL/TLS and AES to protect data both in transit and at rest.
- Implement Access Controls: Restrict access to sensitive data based on user roles, permissions, and need-to-know principles.
- Regularly Update Software and Patches: Keep software up-to-date with the latest security patches to prevent exploitation of known vulnerabilities.
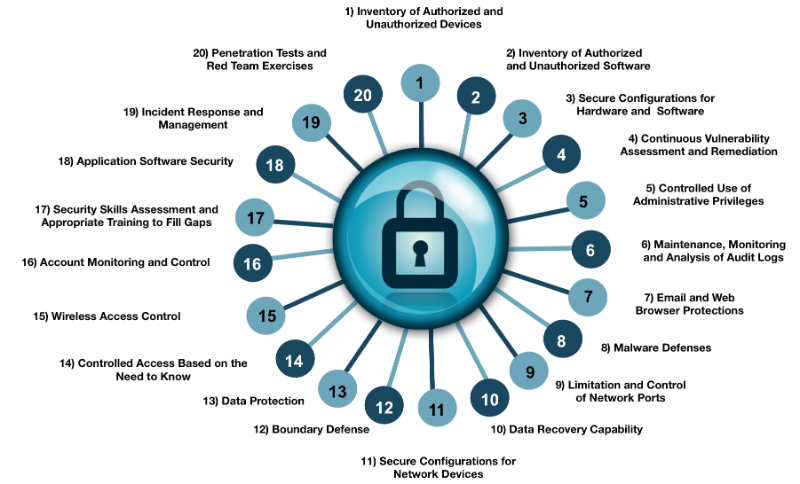
- Conduct Regular Security Audits and Penetration Testing: Perform regular security audits and penetration testing to identify vulnerabilities and weaknesses.
- Implement Data Loss Prevention (DLP) Solutions: Use DLP solutions to monitor and control data access, use, and transfer.
Conclusion
Securing online critical data is an ongoing process that requires dedication and vigilance. By following the best practices outlined in this guide, organizations can protect sensitive information from cyber threats and ensure the confidentiality, integrity, and availability of critical data.
Additional Resources
For more information on securing online critical data, check out the following resources:
- CISA's Cybersecurity Best Practices
- NIST's Cybersecurity Framework
- GDPR Guidance
- PCI-DSS Compliance
- Cisco's Critical Security Controls
Stay informed about the latest cybersecurity threats and best practices by visiting reputable sources like CISA, NIST, and industry-leading cybersecurity websites.