Online Data Encryption Methods: A Comprehensive Guide to Protect Your Data
What is Online Data Encryption?
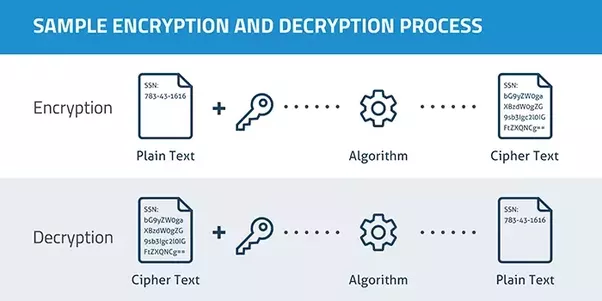
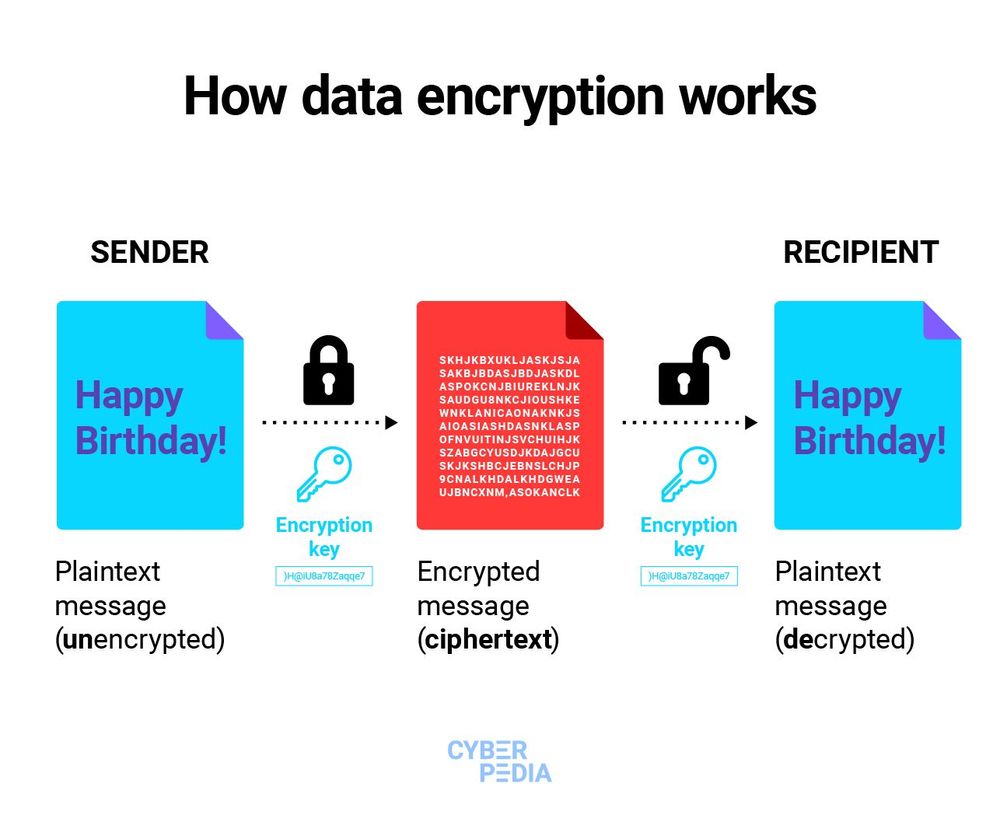
Online data encryption refers to the process of converting sensitive information into a secret code to prevent unauthorized access. This is a crucial aspect of data security, as it helps protect sensitive data from being accessed by hackers, cyber thieves, and other malicious individuals.
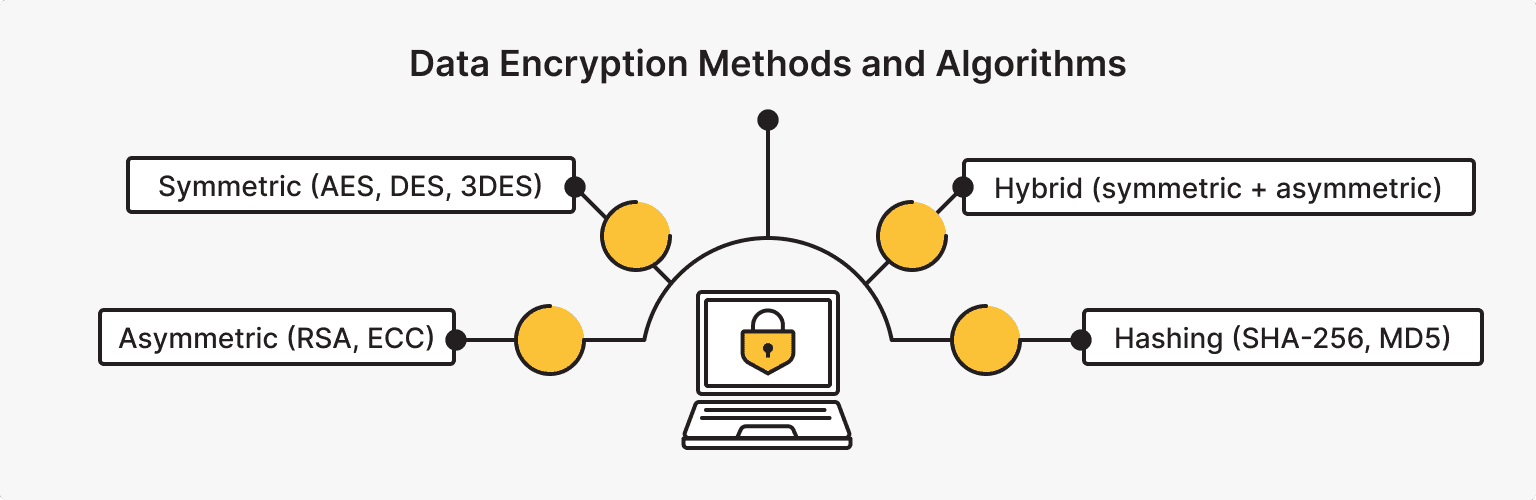
Types of Online Data Encryption Methods
There are several types of online data encryption methods, including:
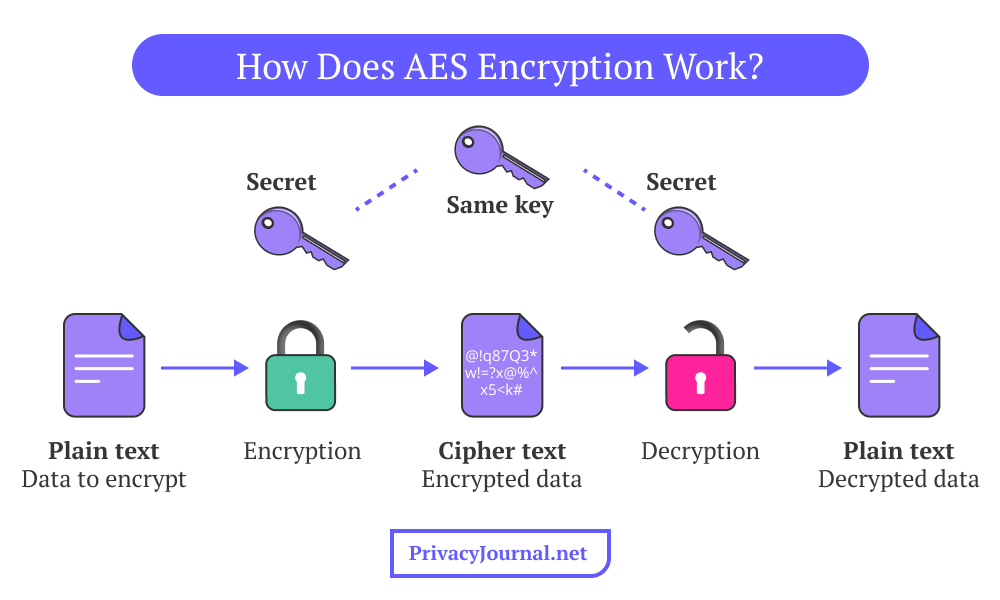
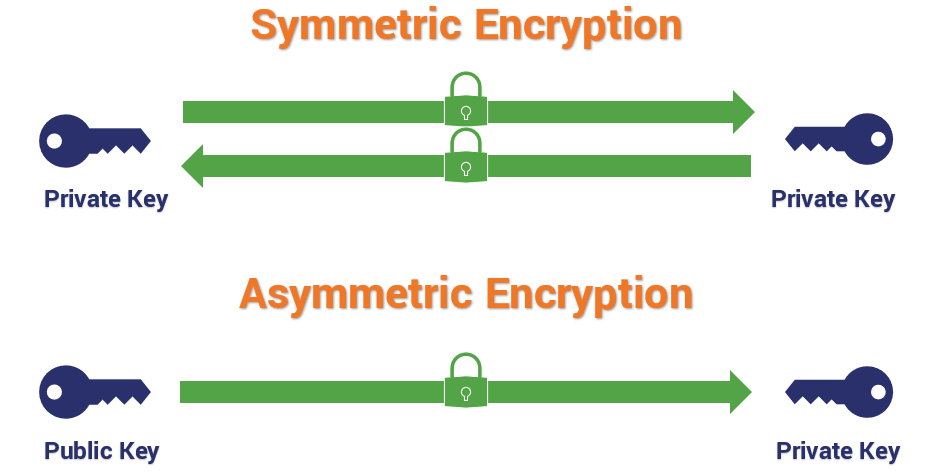
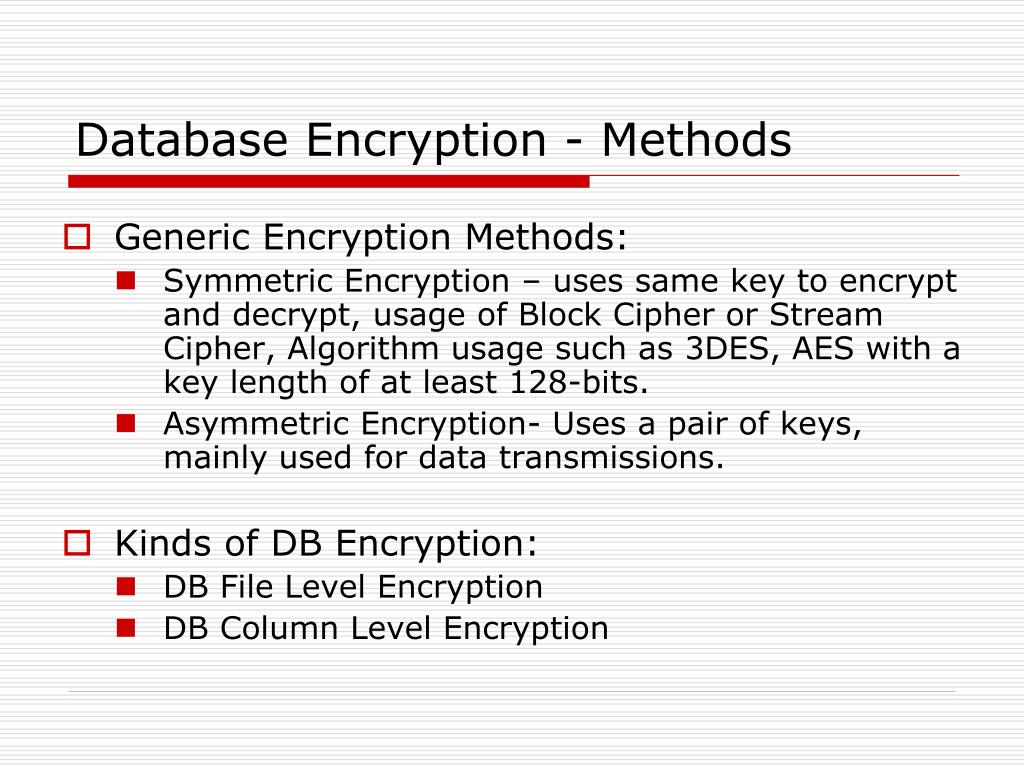
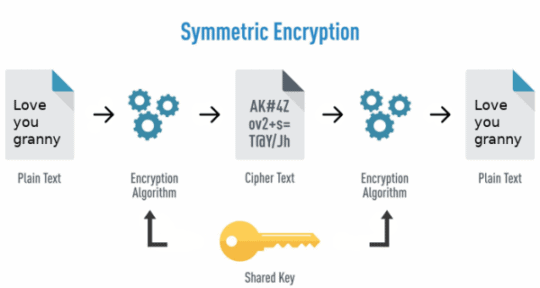
- Symmetric Encryption: This method uses the same key for both encryption and decryption. It is faster and more efficient than asymmetric encryption but offers less security.
- Asymmetric Encryption: This method uses a pair of keys, a public key for encryption and a private key for decryption. It is slower and less efficient than symmetric encryption but offers better security.
- Block Ciphers: These are encryption algorithms that encrypt data in fixed-length blocks. They are commonly used in symmetric encryption and offer better security than stream ciphers.
- Stream Ciphers: These are encryption algorithms that encrypt data in a continuous stream. They are commonly used in symmetric encryption and offer better security than block ciphers.
- Hash Functions: These are one-way encryption algorithms that take input data and produce a fixed-length hash value. They are commonly used for password storage and offer better security than encryption algorithms.
Benefits of Online Data Encryption Methods
The benefits of online data encryption methods include:
- Data Protection: Online data encryption methods protect sensitive data from unauthorized access and data breaches.
- Compliance: Online data encryption methods help organizations comply with relevant data protection regulations and laws.
- non-repudiation: Online data encryption methods ensure non-repudiation, which means that the sender cannot deny sending a message.
- Integrity: Online data encryption methods ensure the integrity of sensitive data, meaning that it cannot be tampered with or altered.
Best Practices for Online Data Encryption Methods
Here are some best practices for online data encryption methods:
- Use Strong Keys: Use strong, unique keys for encryption and decryption.
- Use Secure Communications: Use secure communication protocols, such as HTTPS or SFTP, to encrypt data in transit.
- Use Data at Rest Encryption: Encrypt data at rest, even when it is stored in databases or files.
- Use Data in Transit Encryption: Encrypt data in transit, using protocols such as TLS or IPSEC.
- Regularly Update and Maintain: Regularly update and maintain your online data encryption methods to ensure they remain secure and effective.
Conclusion
Online data encryption methods are a crucial aspect of data security, providing protection for sensitive data from unauthorized access and data breaches. By understanding the different types of online data encryption methods, their benefits, and best practices, you can help protect your data and ensure compliance with relevant data protection regulations and laws.