Understanding Single Sign on (SSO) Security
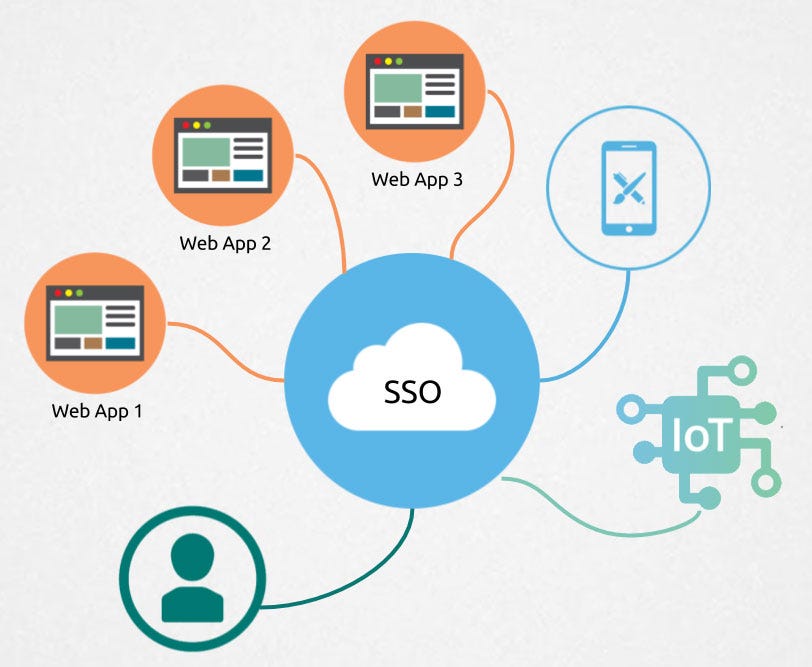
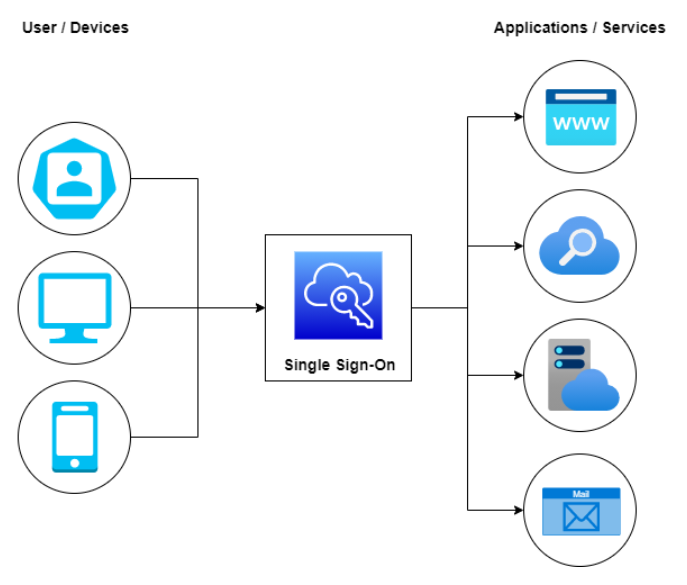
Single Sign on (SSO) security is an essential cloud security technology that simplifies user access by reducing all user application logins to one login, providing greater security and convenience.
What is Single Sign on (SSO) Security?
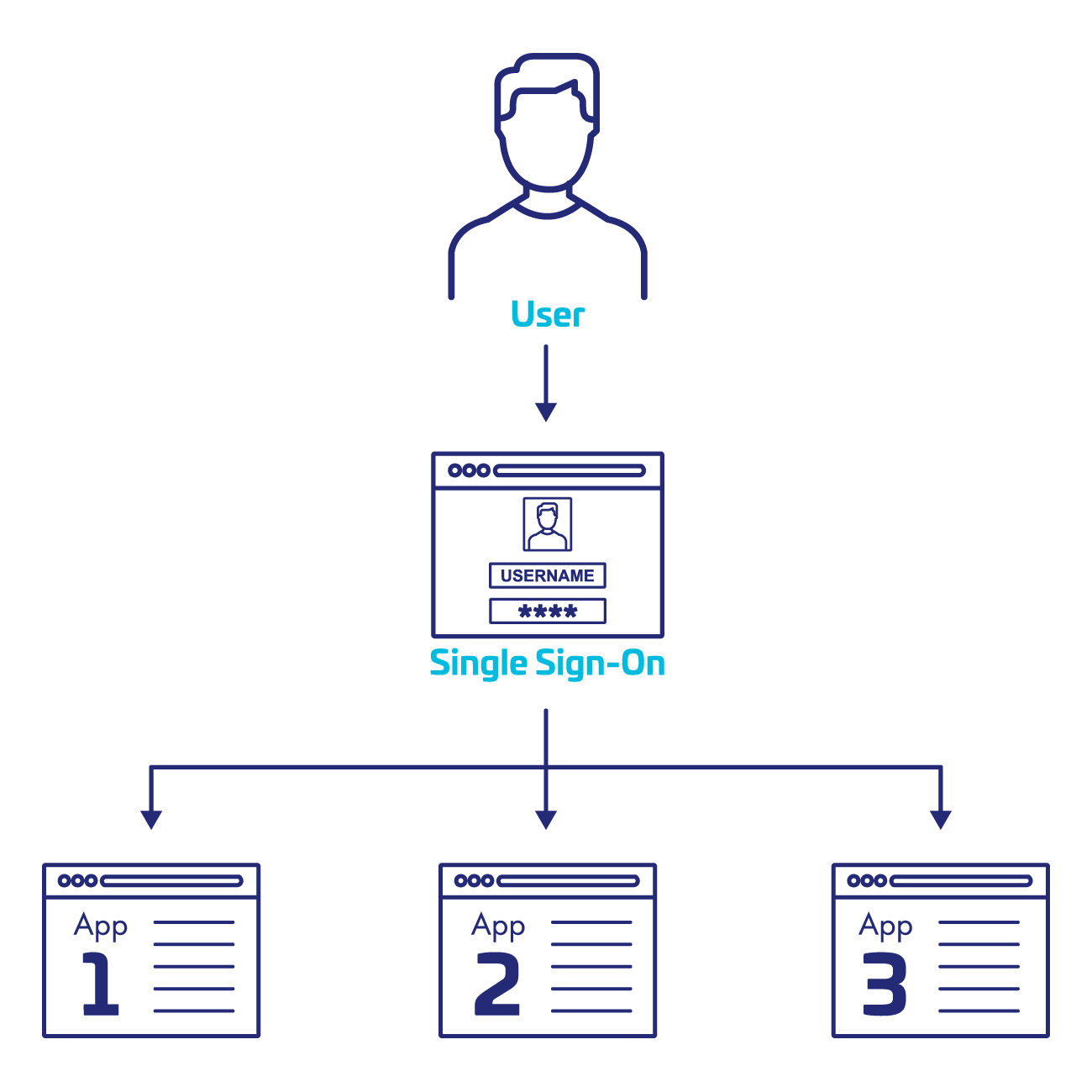
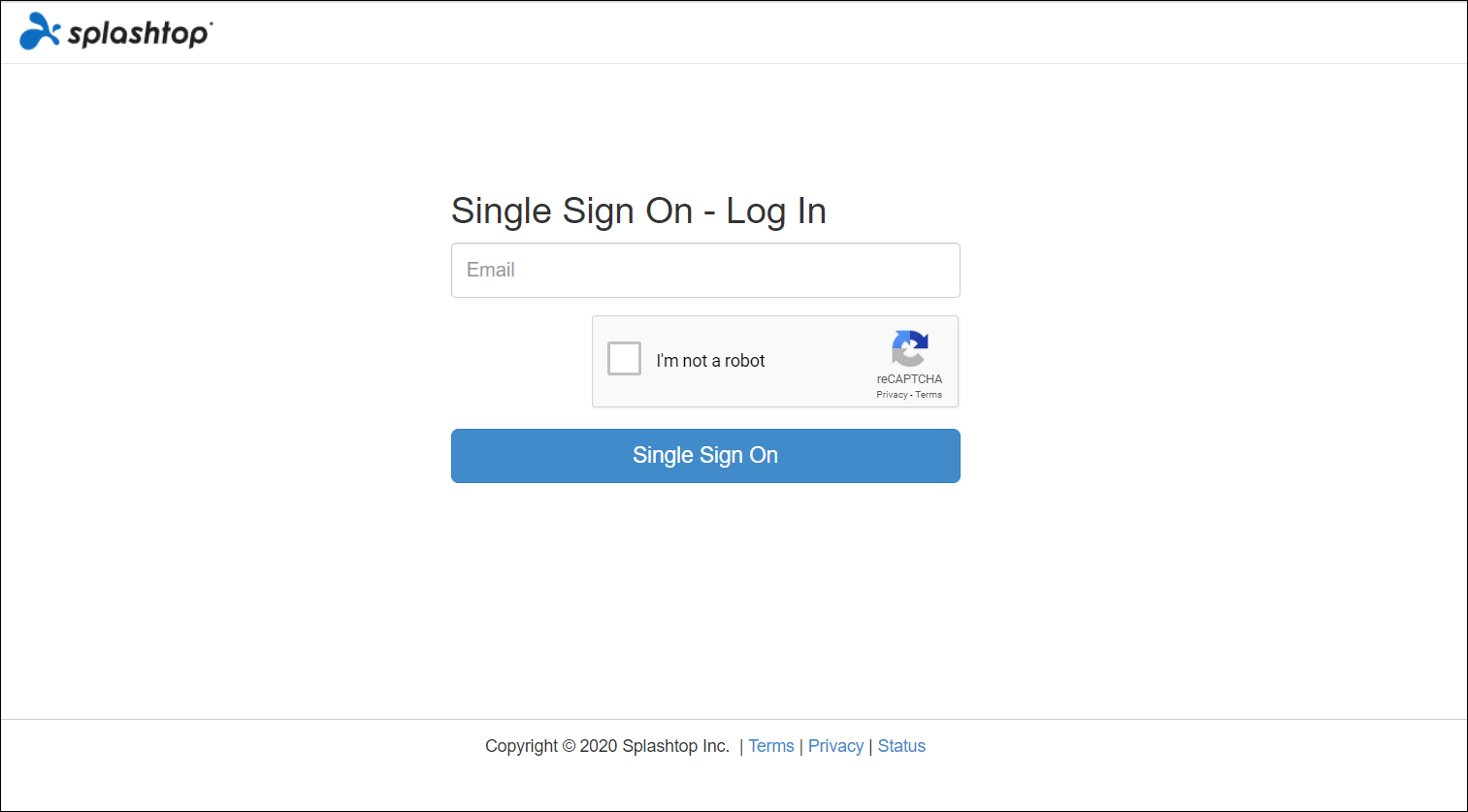
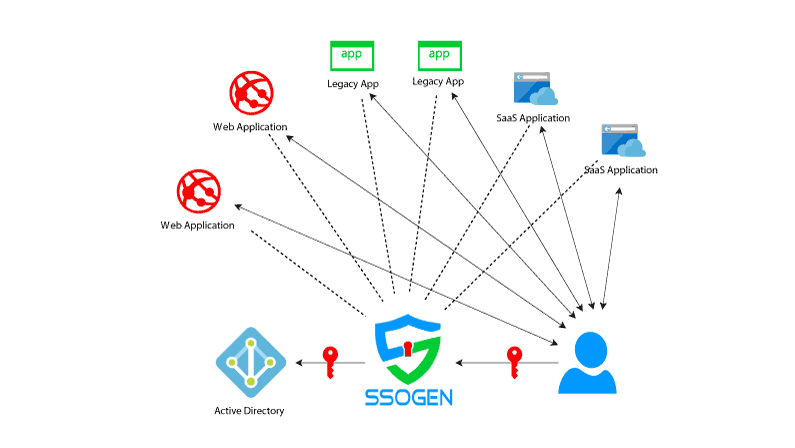
Single Sign on (SSO) is an authentication scheme that allows a user to log in with a single ID to any of several related, yet independent, software systems. This technology centralizes authentication through an identity provider (IdP), enabling users to sign in once and gain access to approved apps without re-authenticating each time.
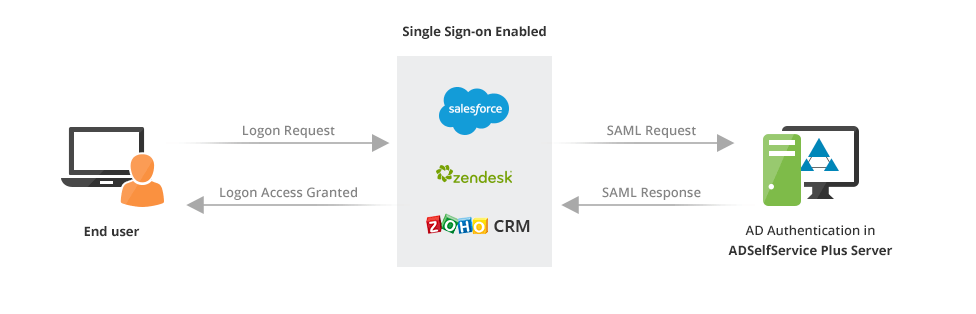
How Does Single Sign on (SSO) Work?
The Single Sign on (SSO) process involves the following steps:
- Identity provider (IdP) authenticates the user's credentials.
- IdP generates a token or certificate containing user information and sends it to the service provider (SP).
- SP verifies the user's identity by checking the token or certificate.
- Once verified, SP grants access to the user, eliminating the need for repeated authentication.
Benefits of Single Sign on (SSO) Security
The benefits of implementing Single Sign on (SSO) security include:
- Improved user experience: Users can access multiple applications with a single set of credentials.
- Enhanced security: Centralized authentication reduces the risk of password fatigue and eliminates the need for users to remember multiple passwords.
- Increased productivity: Users can access all necessary applications without having to re-authenticate each time.
- Reduced administrative efforts: IT teams can manage user access and authentication from a single location.
Challenges and Risks of Single Sign on (SSO) Security

While Single Sign on (SSO) security offers numerous benefits, it also introduces several challenges and risks, including:
- Security risks: Compromised SS0 accounts can grant attackers wide access to your network.
- Single point of failure: If the IdP is compromised, access to all applications may be denied.
- Compliance and regulatory issues: Depending on the organization's industry and location, SSO may not meet required standards.
Best Practices for Implementing Single Sign on (SSO) Security
To ensure secure Single Sign on (SSO) implementation, follow these best practices:
- Combine SSO with multi-factor authentication (MFA) to strengthen access security.
- Use strong password hygiene and security awareness training to educate users about SSO best practices.
- Implement web filtering to prevent unauthorized access to sensitive data.
- Regularly monitor and log user activities to detect potential security threats.
- Use reputable and secure identity providers (IdP) to ensure the integrity of the SSO process.
Alternatives to Single Sign on (SSO) Security
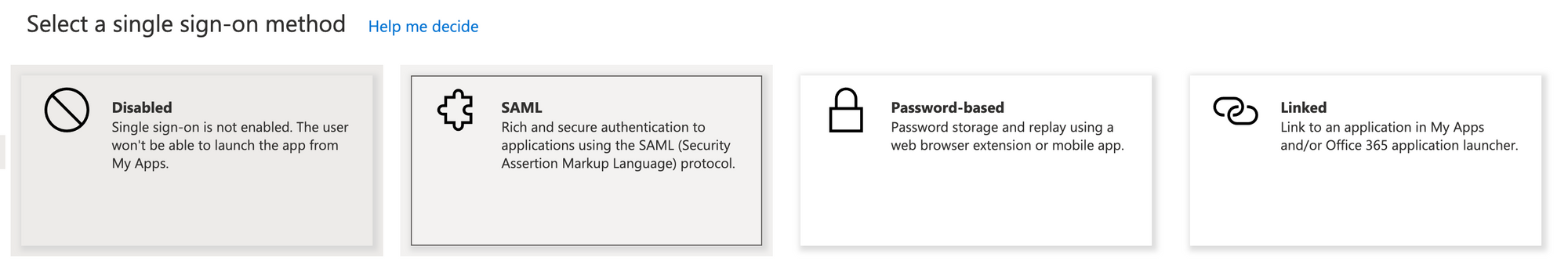
While Single Sign on (SSO) offers numerous benefits, it may not be the best solution for every organization. Consider the following alternatives:
- Multi-factor authentication (MFA): Provides an additional layer of security for users accessing sensitive applications.
- Passwordless authentication: Eliminates the need for passwords altogether, providing a seamless user experience.
- Identity and access management (IAM): Offers a comprehensive solution for managing user access and authentication across multiple applications.
Conclusion
Single Sign on (SSO) security is a powerful cloud security technology that simplifies user access while providing greater security and convenience. By understanding the benefits, challenges, and best practices for implementing SSO security, organizations can make informed decisions about their security infrastructure and protect their users, applications, and data from potential threats.