Securing Application Security Jay anti malware: Best Practices for Java Cybersecurity
Cybersecurity is a critical concern for Java applications, given the increasing number of cyberattacks targeting software vulnerabilities. As a developer or administrator, it's essential to follow best practices for Java cybersecurity to protect your applications and sensitive data. In this article, we'll explore the importance of securing application security Jay anti malware and provide guidelines for implementing robust protection strategies.
Understanding Java Cybersecurity Risks
Cyberattacks can exploit vulnerabilities in Java applications, allowing attackers to inject malicious code, steal sensitive data, or disrupt system functionality. Common Java security risks include:
- Injection attacks: inserting malicious code into input fields or databases
- Man-in-the-middle attacks: intercepting and altering communication between users and applications
- Malware and ransomware attacks: compromising system integrity and demanding payment for decryption
Secure Coding Practices for Java Applications
To mitigate Java security risks, developers should follow secure coding practices, including:
- Input validation and sanitization: verifying and filtering user input to prevent malicious code injection
- Error handling and logging: logging errors and exceptions to detect potential security issues
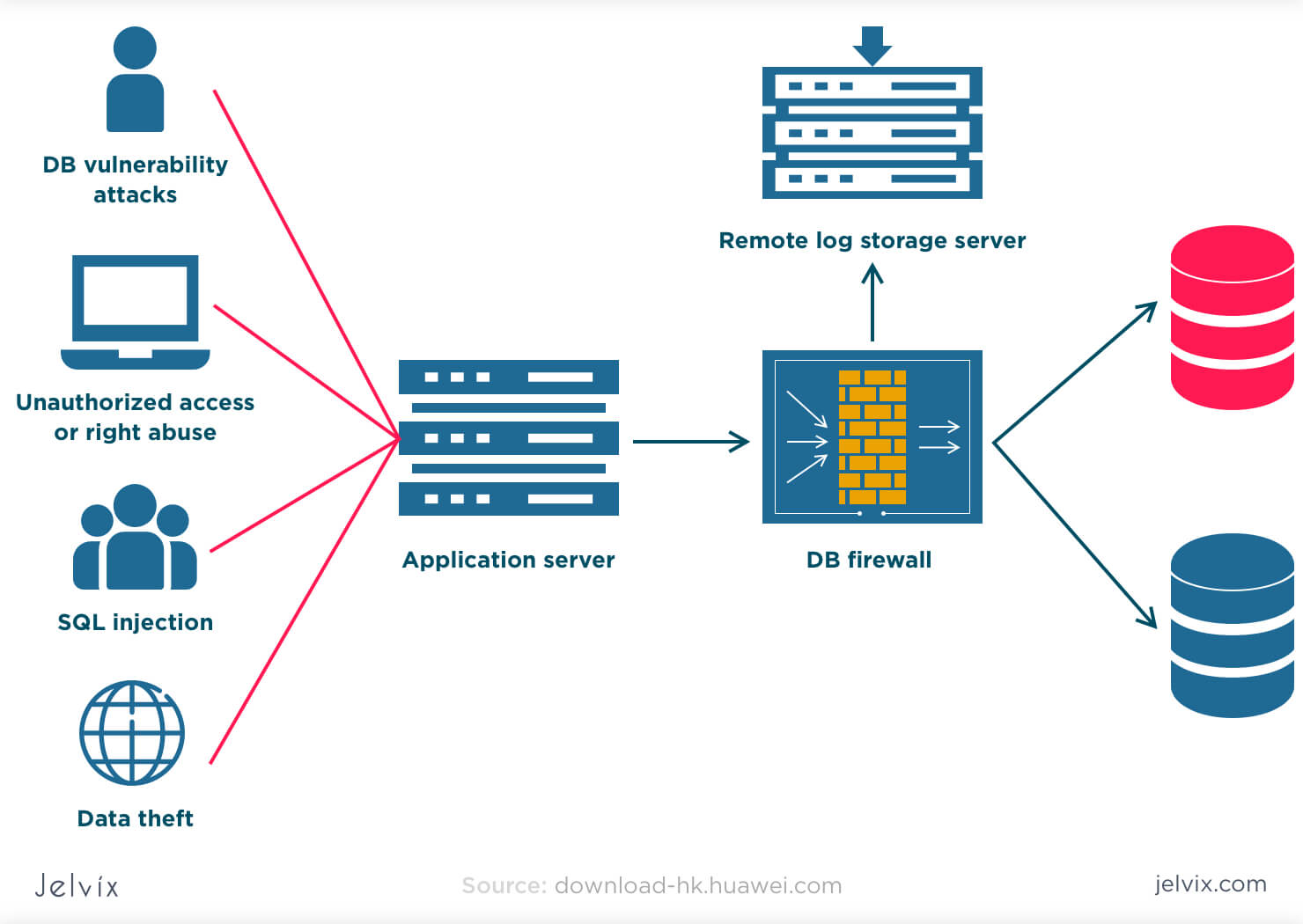
- Secure data storage: encrypting sensitive data and following best practices for database security
- Regular code reviews and testing: identifying and addressing security vulnerabilities through code reviews and testing
Implementing Robust Protection Strategies
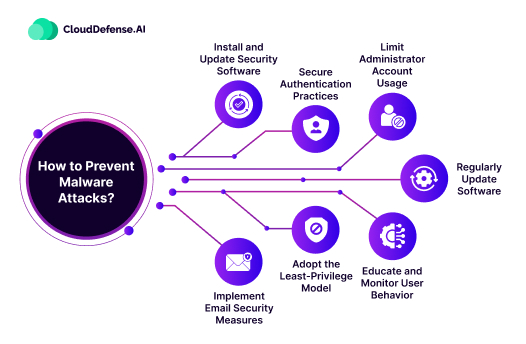
To further enhance Java application security, consider implementing the following protection strategies:

- Use a reputable anti-malware solution, such as Jay anti malware, to detect and remove malware
- Implement a web application firewall (WAF) to filter incoming traffic and block known security threats
- Use secure communication protocols, such as SSL/TLS, to encrypt data in transit
- Regularly update and patch Java applications to address known security vulnerabilities
Monitoring and Incident Response
Regularly monitoring Java applications and having an incident response plan in place is crucial to detecting and responding to security incidents. This includes:
- Implementing logging and monitoring tools to detect security incidents
- Developing an incident response plan to address security incidents quickly and effectively
- Providing training and awareness programs for developers and administrators to educate them on Java security best practices
Conclusion
Securing application security Jay anti malware is a critical concern for Java developers and administrators. By following secure coding practices, implementing robust protection strategies, and monitoring Java applications, you can significantly reduce the risk of cyberattacks and protect sensitive data. Remember, cybersecurity is an ongoing process that requires continuous effort and attention to stay ahead of evolving threats.
Recommended Resources
For further information on Java security, consider the following resources:
- Oracle Java Security Guidelines
- OWASP Java Security Project
- Jay anti malware documentation







![10 Best Malware Protection Solutions [2026] | NinjaOne 10 Best Malware Protection Solutions [2026] | NinjaOne](https://image.slidesharecdn.com/fakemalwareandvirusscanners-120218104945-phpapp02/85/Fake-malware-and-virus-scanners-15-638.jpg)