Preventing Ransomware On Network Devices: A Comprehensive Guide
With the rapid growth of malware threats, organizations are facing significant challenges in ensuring the security of their networks. Ransomware is the fastest growing malware threat, targeting users of all types, from home users to corporate networks. In this article, we will explore the key strategies to prevent ransomware on network devices.
Why Preventing Ransomware is Crucial
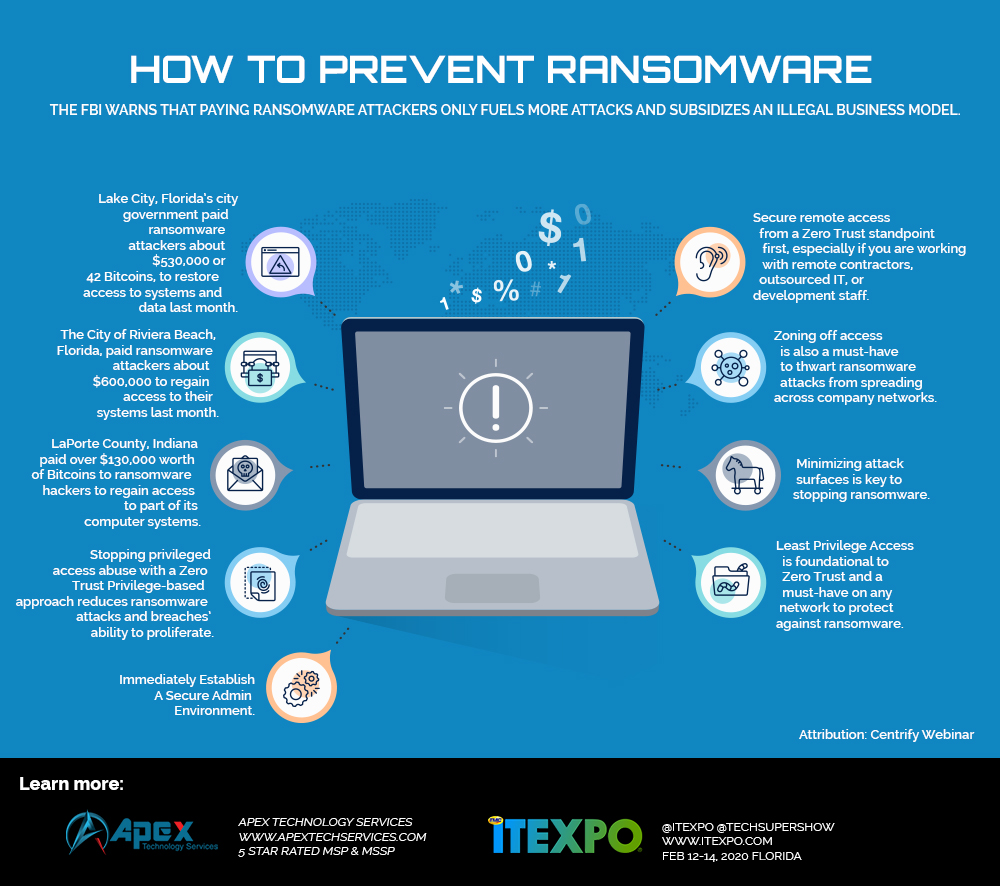
Ransomware is a form of malware that encrypts files or stops users from accessing their computers until a ransom is paid. According to recent statistics, over 4,000 ransomware attacks have occurred daily since January 1, 2016. This represents a 300% increase over the approximately 1,000 attacks per day seen in 2015. The consequences of a ransomware attack can be devastating, including financial loss, damage to reputation, and compromise of sensitive data.
Best Practices for Preventing Ransomware
Preventing ransomware requires a multi-layered approach that encompasses both technological measures and behavioral adjustments. Here are some effective strategies to prevent ransomware on network devices:
- Network Segmentation: Network segmentation divides a network into isolated segments to reduce attack spread and enforce security policies. This limits lateral movement during attacks and separates sensitive systems from general access.
- Immutable Backups: Regular backups are essential in recovering from a ransomware attack. However, they must be immutable and stored offline to prevent encryption by the malware.
- Strong Authentication: Implementing strong authentication measures, such as multi-factor authentication (MFA), can prevent unauthorized access to network devices and reduce the risk of ransomware attacks.
- Staff Training: Regular security training for all staff members helps prevent the phishing attacks that initiate most ransomware incidents.
Traditional Endpoint Security vs. Network Share Protection
Traditional endpoint security focuses on protecting individual devices, while Network Share Protection safeguards shared data itself, preventing ransomware from encrypting files on network drives even if the attack originates from another device on the network.
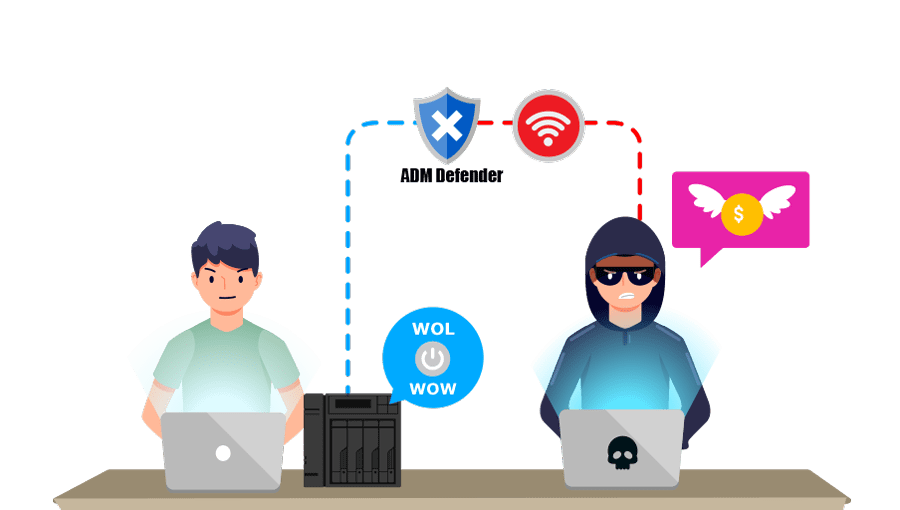
VPN and Remote Access Management
Secure VPN connections and remote access management are also essential to prevent ransomware attacks. This includes implementing strict access controls, such as identity-based access controls and two-factor authentication.
Monitoring and Incident Response
Regular network monitoring and incident response planning are critical in detecting and responding to ransomware attacks. This includes implementing system event logging, network traffic monitoring, and incident response playbooks.
Power Down Devices
When unable to disconnect a device from the network to avoid further spread of the ransomware infection, power it down. This step will prevent your organization from maintaining ransomware infection artifacts and potential evidence stored in volatile memory.
Conclusion
Preventing ransomware on network devices requires a comprehensive approach that encompasses both technological measures and behavioral adjustments. By implementing these strategies, organizations can significantly reduce the risk of ransomware attacks and ensure the security and integrity of their data.
Learn More About Ransomware Prevention
For more information on ransomware prevention and best practices, please refer to the following resources: