Implementing Data Loss Prevention: Best Practices for a Robust DLP Deployment
In today's digital landscape, data loss prevention (DLP) has become a critical component of any organization's cybersecurity strategy. Every business needs a unique approach to DLP, as each organization's goals, resources, and situation are distinct. However, there are common elements that successful DLP implementations share. This article presents the best practices for planning a DLP deployment.
Understanding Data Loss Prevention
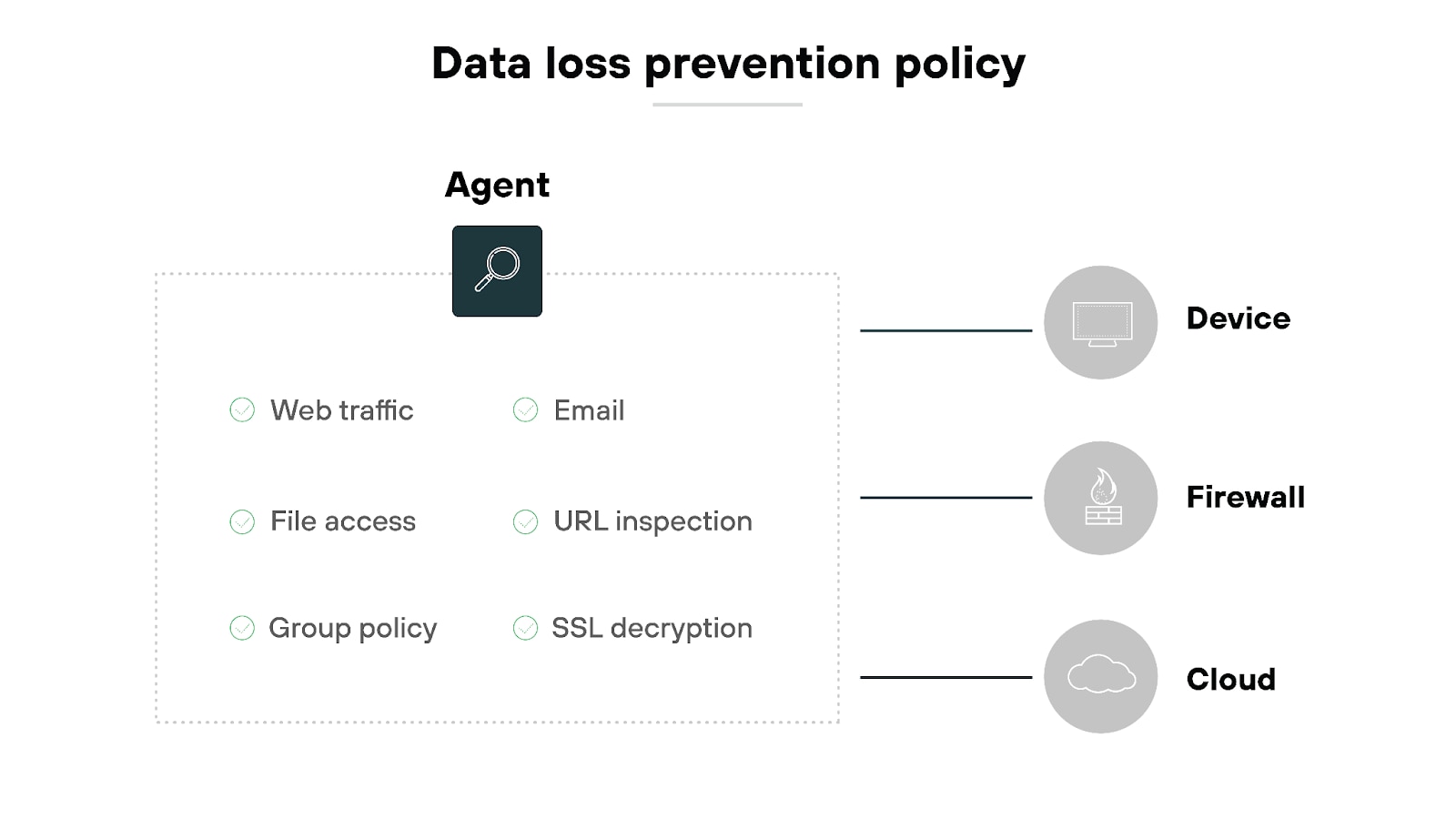
Data loss prevention (DLP) is a cybersecurity strategy that uses software tools and policies to detect, monitor, and block sensitive data from being accessed, shared, or transferred without authorization. DLP solutions identify and prevent the unauthorized sharing, transfer, and use of sensitive data, addressing data risk in modern businesses.
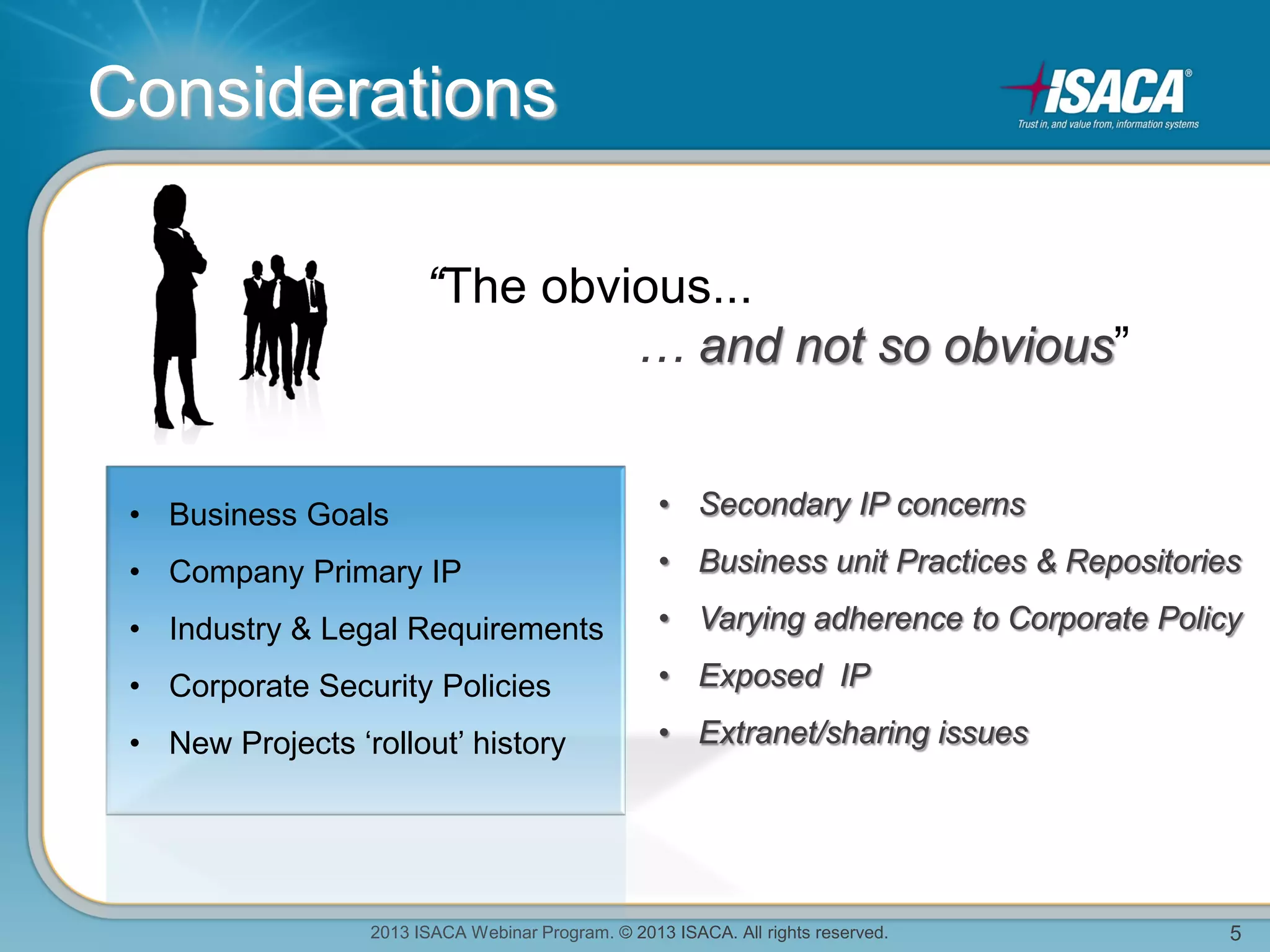
Key Elements of a Successful DLP Implementation
A successful DLP implementation involves several key elements, including:
-
Identification of Sensitive Data: DLP solutions must be able to identify sensitive data, including personal identifiable information (PII), financial information, and intellectual property.
-
Data Classification: Organizations must classify their data according to its sensitivity and importance to determine the level of protection required.
-
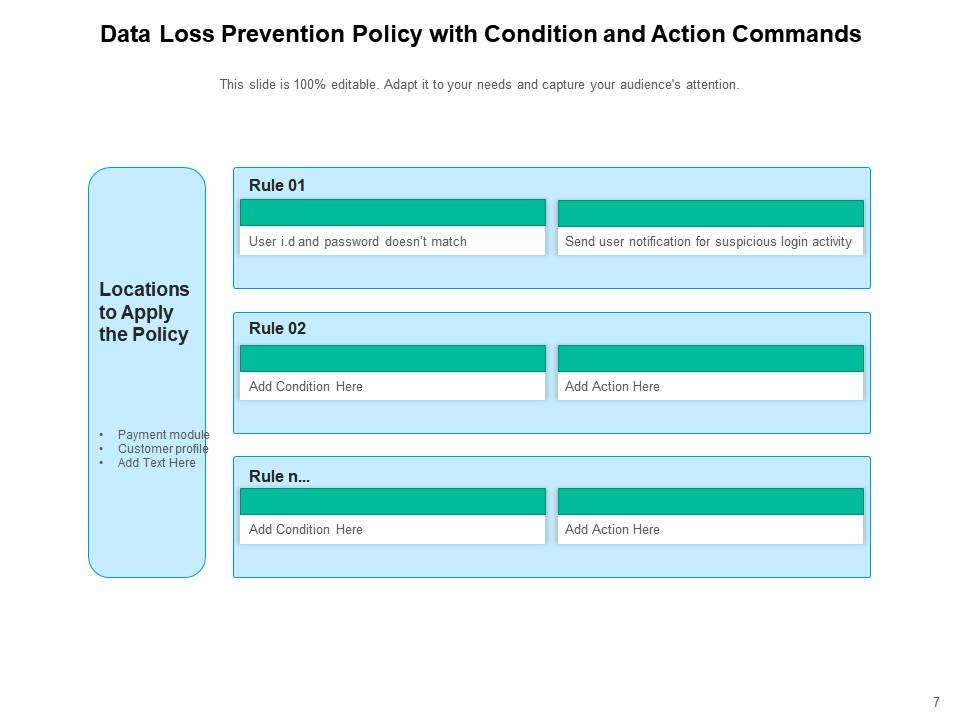
Policy Development: Policies and procedures must be developed to govern the handling and protection of sensitive data.
-
Technology Deployment: DLP solutions must be deployed across the organization, including endpoints, networks, and cloud storage.
-
Ongoing Monitoring and Enforcement: Organizations must continuously monitor and enforce DLP policies to ensure compliance and prevent data breaches.
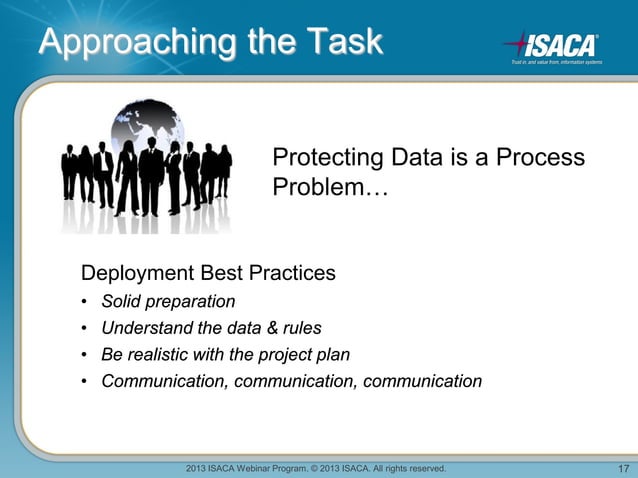
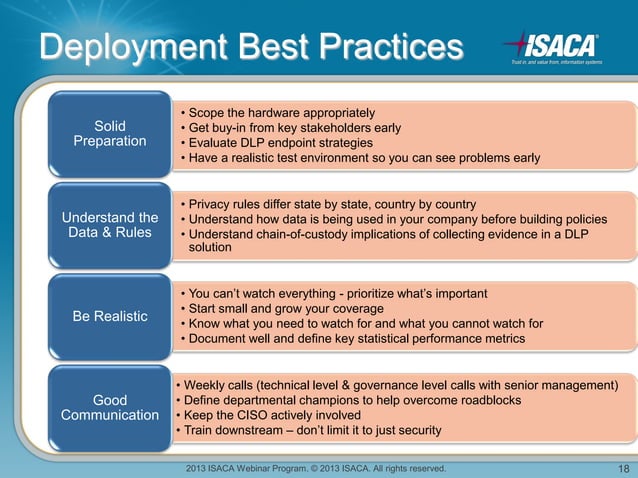
Implementing DLP: A Step-by-Step Guide

Implementing DLP involves several steps, including:
-
Discovery and Classification: Identify sensitive data and classify it according to its sensitivity and importance.
-
Policy Development: Develop policies and procedures to govern the handling and protection of sensitive data.
-
Technology Deployment: Deploy DLP solutions across the organization, including endpoints, networks, and cloud storage.
-
Ongoing Monitoring and Enforcement: Continuously monitor and enforce DLP policies to ensure compliance and prevent data breaches.
-
Training and Awareness: Provide training and awareness programs to educate employees on DLP policies and procedures.
Benefits of Implementing DLP
Implementing DLP offers several benefits, including:
-
Prevention of Data Breaches: DLP solutions can detect and prevent data breaches, reducing the risk of financial losses and reputational damage.
-
Compliance with Regulations: DLP solutions can help organizations comply with data protection regulations, such as GDPR and HIPAA.
-
Protection of Sensitive Data: DLP solutions can protect sensitive data from unauthorized access, use, or transfer.
-
Improved Employee Productivity: DLP solutions can help employees work more efficiently and effectively by reducing the time spent on data-related tasks.
Conclusion
Implementing DLP is a critical component of any organization's cybersecurity strategy. By following the best practices outlined in this article, organizations can implement a robust DLP deployment that protects sensitive data, prevents data breaches, and ensures compliance with regulations. Remember, a successful DLP implementation requires ongoing monitoring and enforcement to ensure the protection of sensitive data.