Protecting against Malware on IoT Devices: A Comprehensive Guide
Introduction
The Internet of Things (IoT) has revolutionized the way we live and work, with billions of connected devices transforming our homes, businesses, and industries. However, this increased connectivity has also created new vulnerabilities, making IoT devices a prime target for malware and cyber attacks. In this article, we will explore the risks associated with IoT malware and provide actionable tips on how to protect against these threats.Understanding IoT Malware
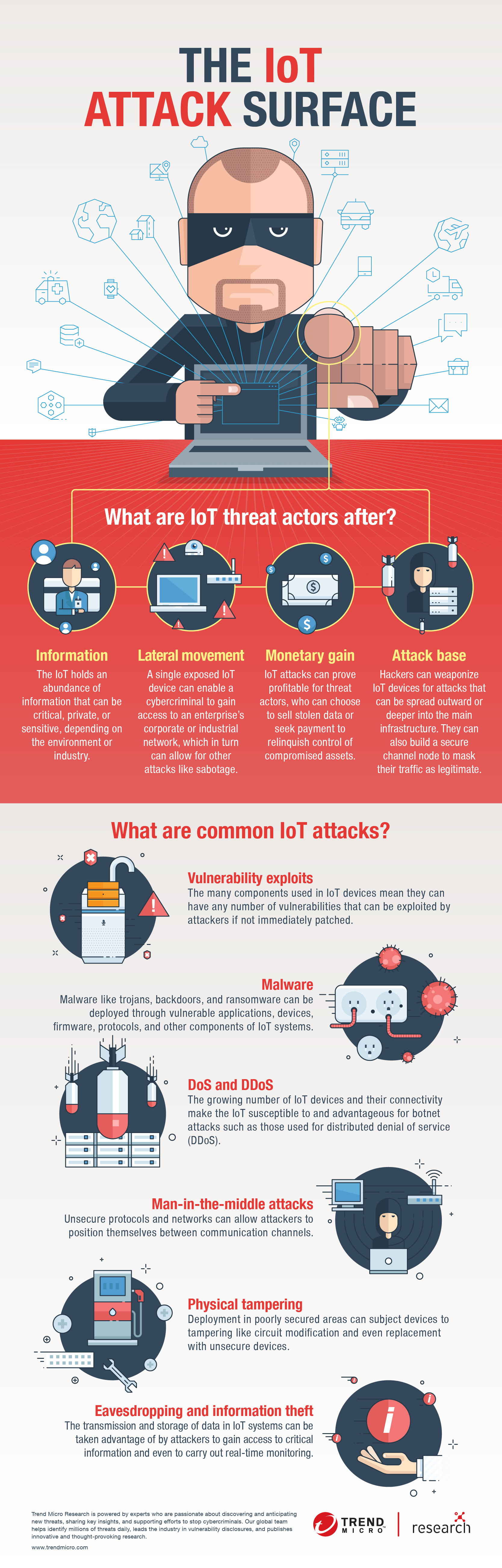
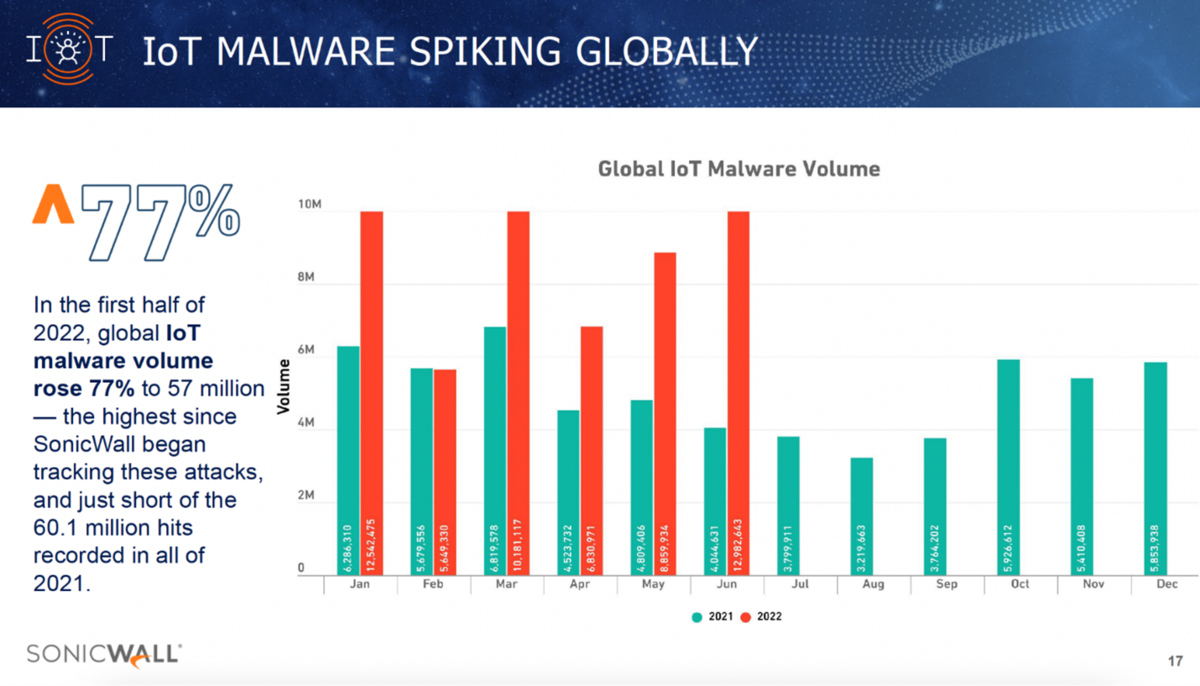
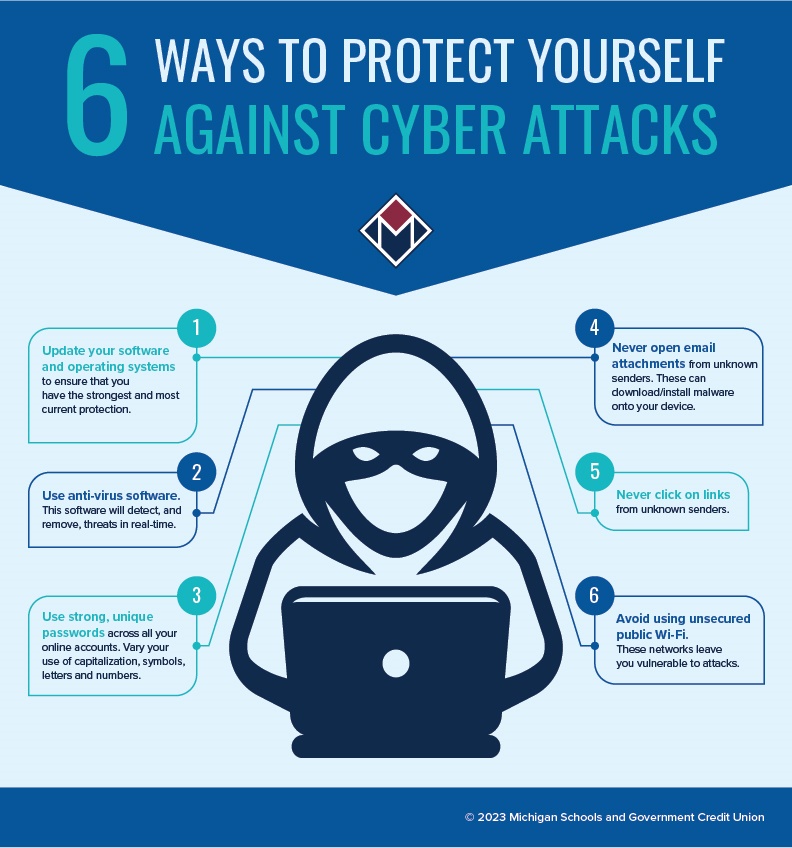
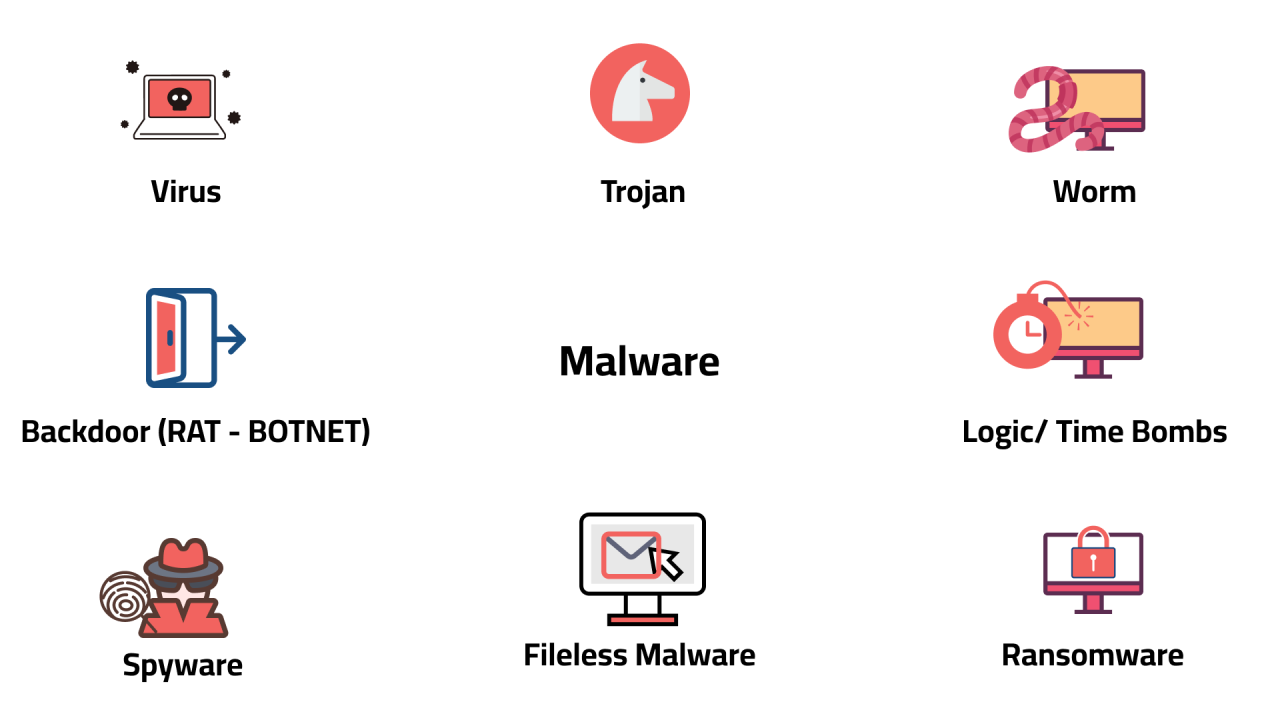
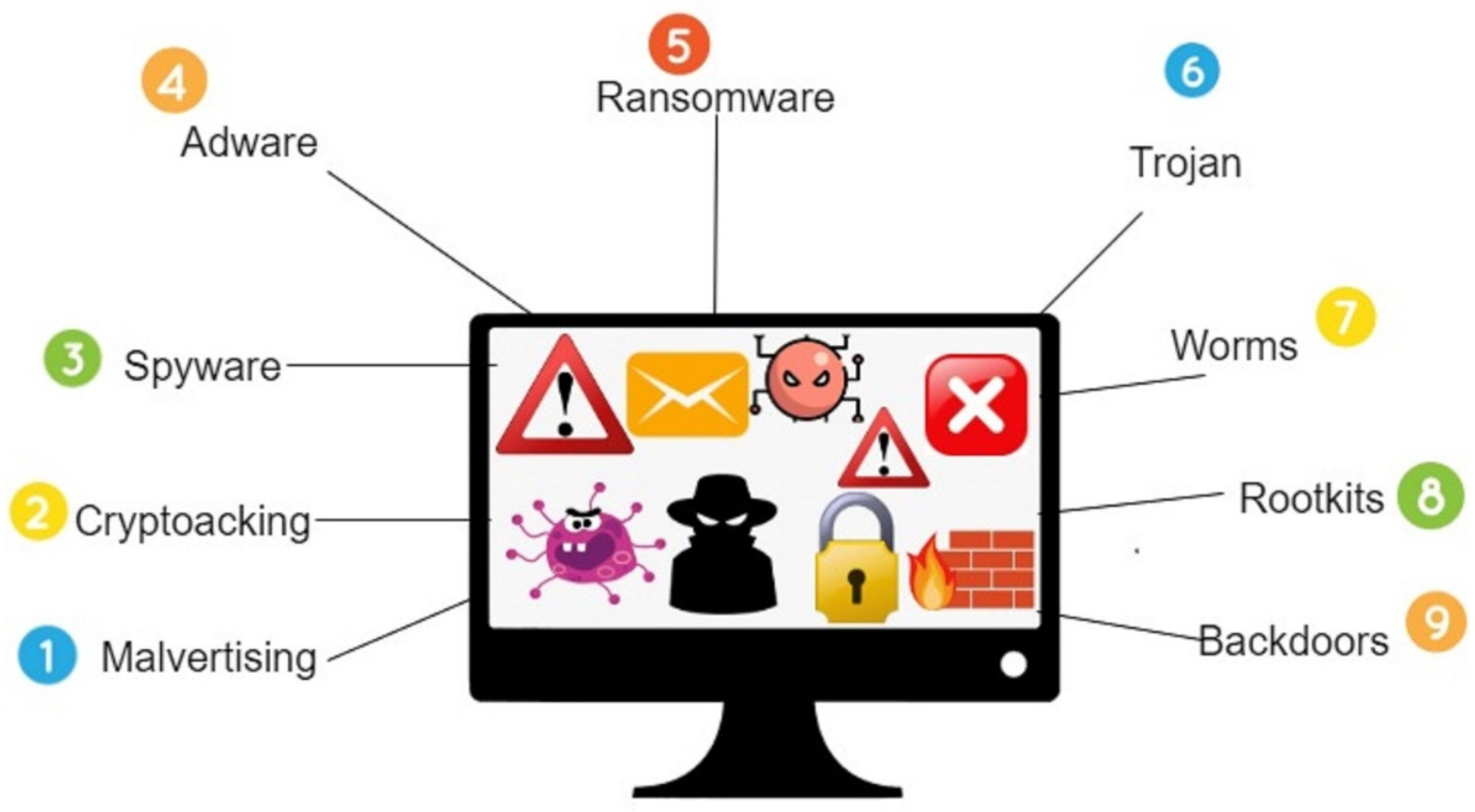
IoT malware refers to malicious software designed to compromise or control IoT devices. These devices, which range from smart home appliances to industrial sensors, are often connected to the internet and can be accessed remotely. Malware can spread rapidly through IoT devices, creating botnets that can be used for various malicious purposes, including data theft, ransomware, and distributed denial-of-service (DDoS) attacks.Why IoT Devices are Vulnerable to Malware