How to Block Malware from Accessing Admin Settings: A Comprehensive Guide
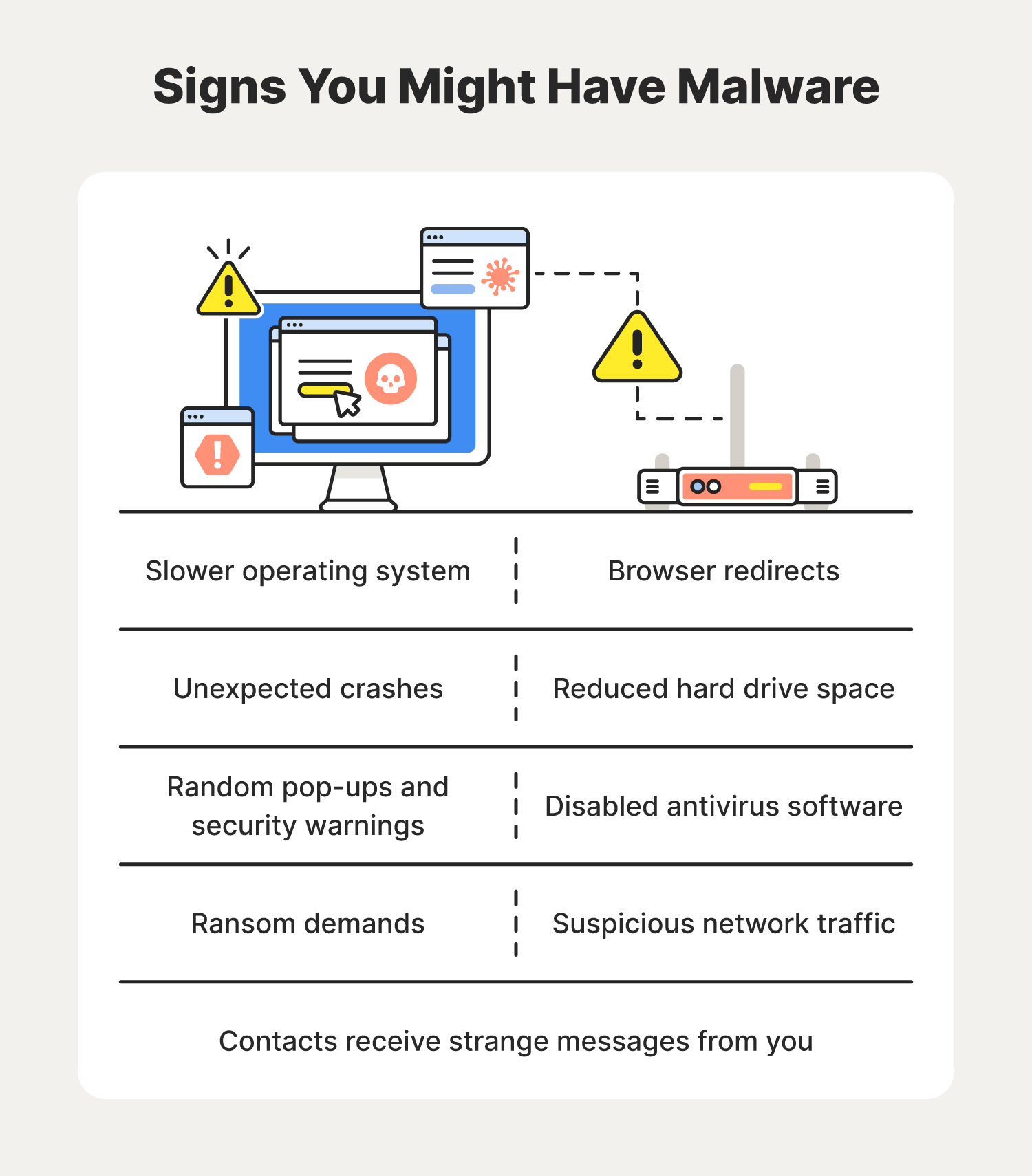
Malware has become a significant threat to the security of our devices, and administrator protection is a crucial aspect of mitigating this threat. In this article, we will discuss how to block malware from accessing admin settings, focusing on the importance of administrator protection, Windows User Account Control (UAC), and additional security settings.
Admin Protection: Stopping Malware in Its Tracks
Admin protection breaks the attack kill chain since malware can no longer silently acquire admin privileges. By removing local administrator rights from Windows endpoints, businesses can reduce malware risks while maintaining application access for enterprise users. This approach prevents installation of unauthorized apps and unintended changes to system settings.
Understanding Windows User Account Control (UAC)
Windows User Account Control (UAC) is a critical protection built into Windows. It prevents silent system-level changes, reduces malware impact, and nudges apps to run with the lowest privileges they actually need. Configured correctly, UAC gives control over what can change the system – and when. This feature should be in the forefront of your mind when evaluating how to block malware from accessing admin settings.
Blocking Malware with Microsoft Defender SmartScreen
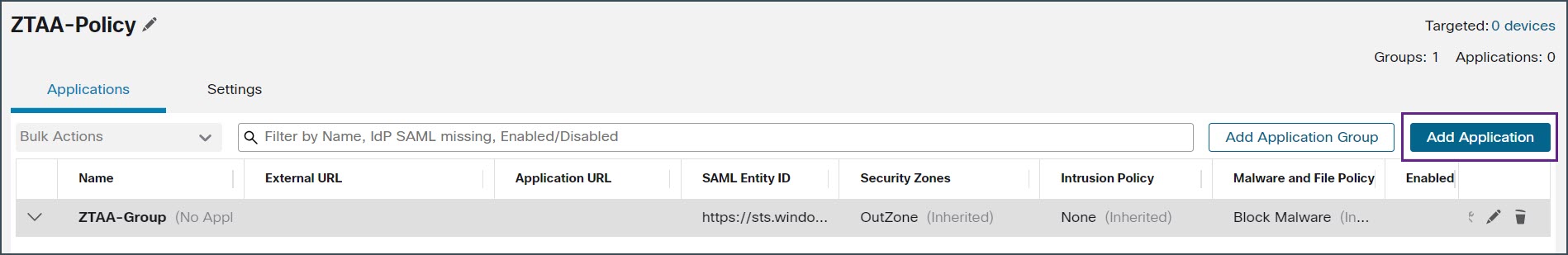
Microsoft Defender SmartScreen is a security feature in Windows that checks apps, files, and websites against Microsoft's threat database to block or warn about phishing, malware, and unverified applications. Admins can configure Microsoft Defender SmartScreen using Group Policy, Microsoft Intune, or mobile device management (MDM) settings. This approach ensures user safety by displaying a warning page and allowing users to continue to the site or blocking the site entirely.
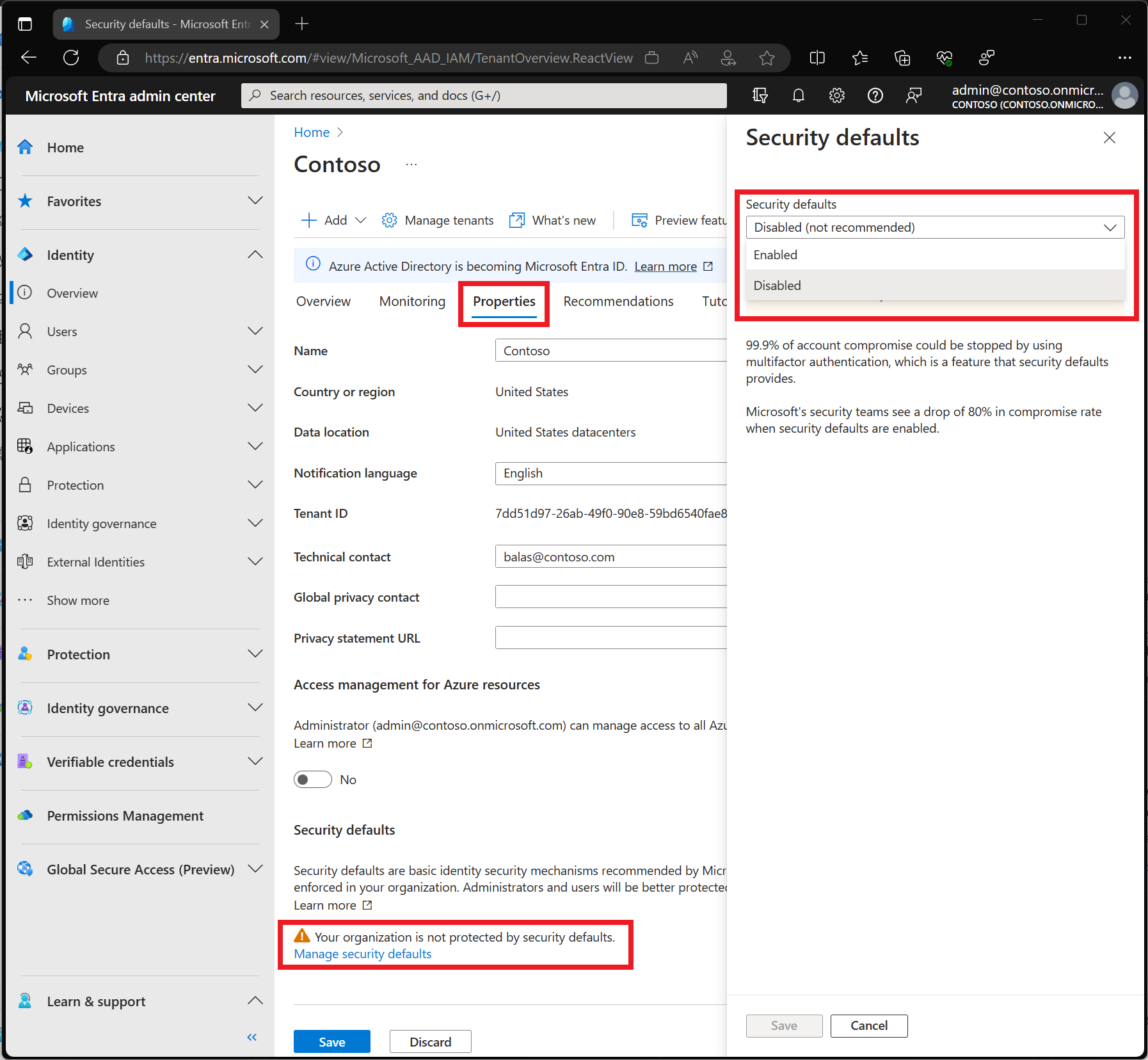
Enabling Administrator Protection in Windows 11
Enabling Administrator Protection in Windows 11 significantly improves security by addressing critical User Account Control (UAC) weaknesses. Unlike UAC's split-token model, where elevated processes share the user's session and can be exploited by malware, Administrator Protection creates a separate, system-managed administrator account (SMAA) that generates isolated, just-in-time admin privileges.
Additional Security Settings
-
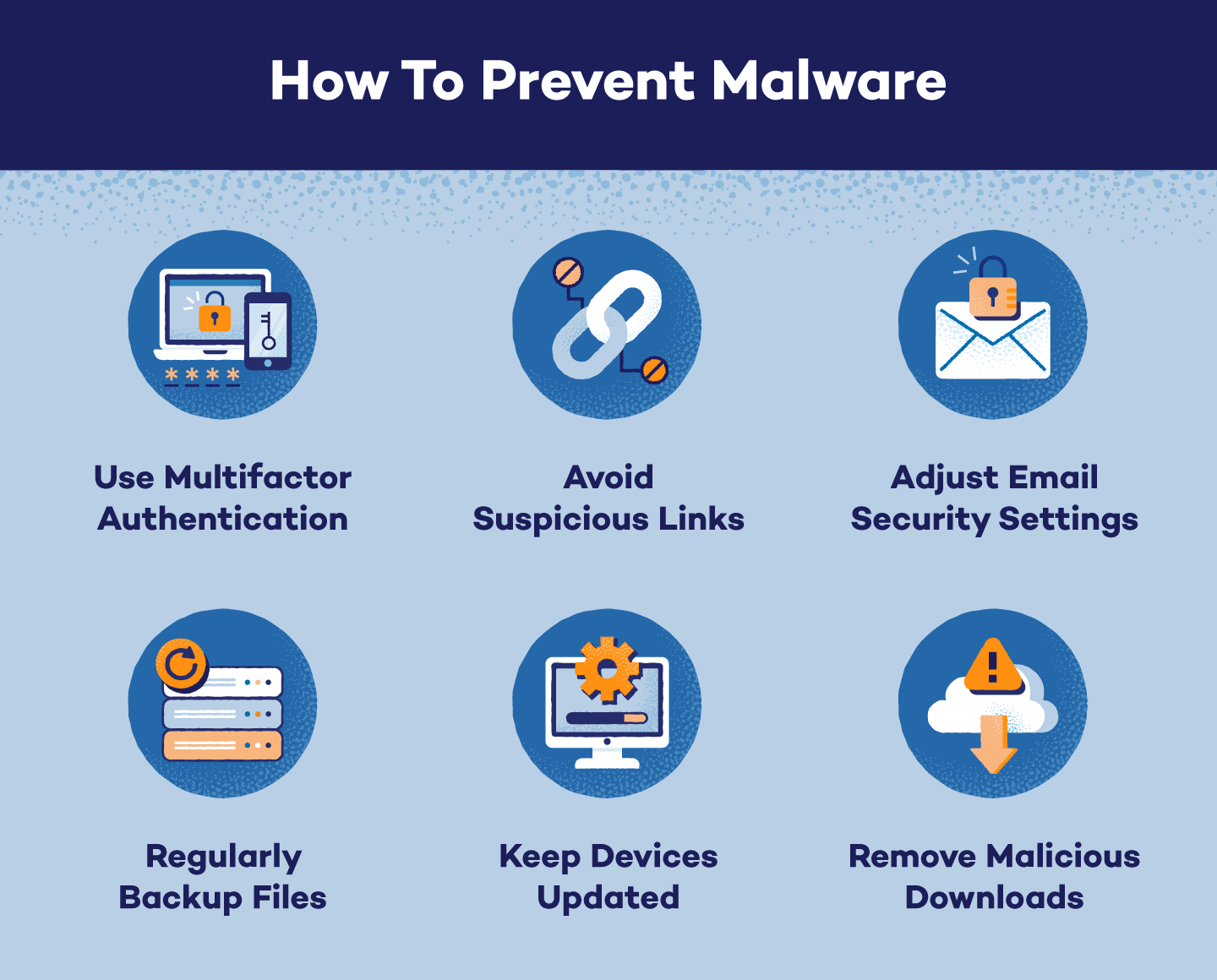
Remove local administrator rights from Windows endpoints to reduce malware risks while maintaining application access for enterprise users.
-
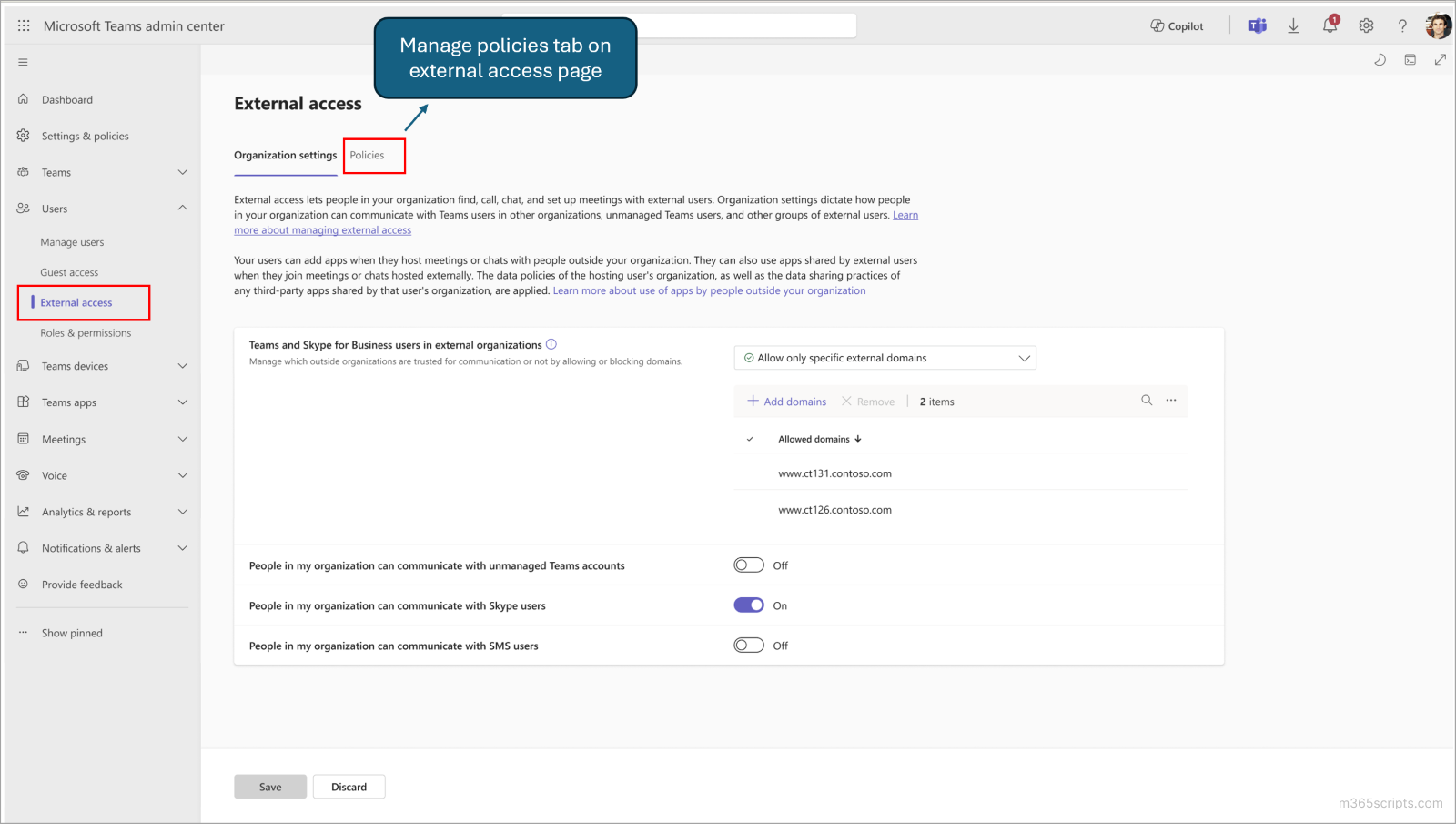
Use web content filtering in Microsoft Defender for Endpoint to track and regulate access to websites based on their content categories.
-
Configure Microsoft Defender SmartScreen using Group Policy, Microsoft Intune, or mobile device management (MDM) settings.
-
Enabling Administrator Protection in Windows 11 creates a separate, system-managed administrator account (SMAA) that generates isolated, just-in-time admin privileges.
-
Consider using a non-administrator account to prevent installation of unauthorized apps and unintended changes to system settings.
Stay Ahead of Malware with Proper Configuration and Administration
By implementing the strategies outlined above, you can block malware from accessing admin settings and protect your device's sensitive information. Effective administrator protection and understanding of Windows User Account Control (UAC) are critical components of this process.
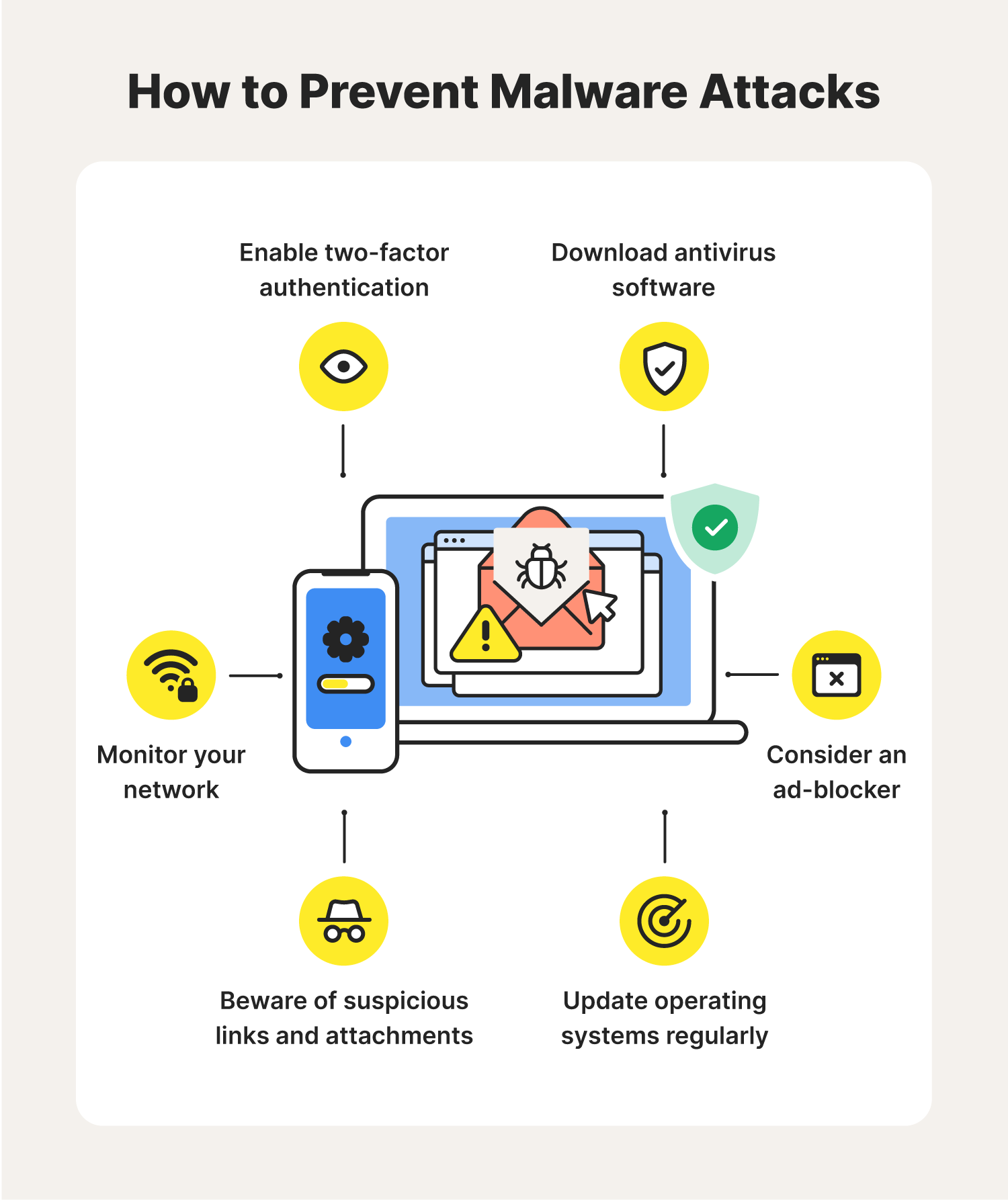
Always keep your software up-to-date, use strong passwords, and employ robust antivirus solutions to ensure the best possible protection. Regularly review and adjust your security settings as necessary to stay ahead of new threats and vulnerabilities.
Protecting your device from malware is a continuous process that requires vigilance and attention to detail. Stay informed, and with this knowledge, you'll be better equipped to block malware from accessing admin settings and keep your digital life safe.