Protecting Confidential Information: A Must for Businesses
Confidential information is a valuable asset for businesses, and protecting it is essential to maintain a competitive edge, prevent identity theft, and ensure compliance with regulations. In today's digital age, sensitive data is easily accessible, and even strong access controls can't fully protect content from hackers or insider leaks if the files themselves aren't locked down.
Why Protect Confidential Information?
Most companies keep sensitive personal information in their files—names, Social Security numbers, credit card, or other account data—that identifies customers or employees. This information often is necessary to fill orders, meet payroll, or perform other necessary business functions. However, if sensitive data falls into the wrong hands, it can lead to fraud, identity theft, or similar problems.
Benefits of Protecting Confidential Information
- Prevents identity theft and fraud
- Preserves a competitive edge
- Ensures compliance with regulations
- Protects trade secrets and confidential business information
- Maintains customer and employee trust
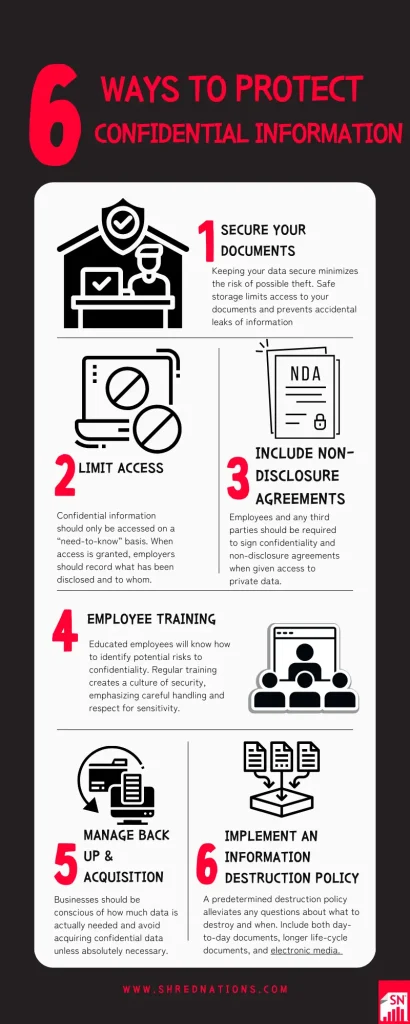
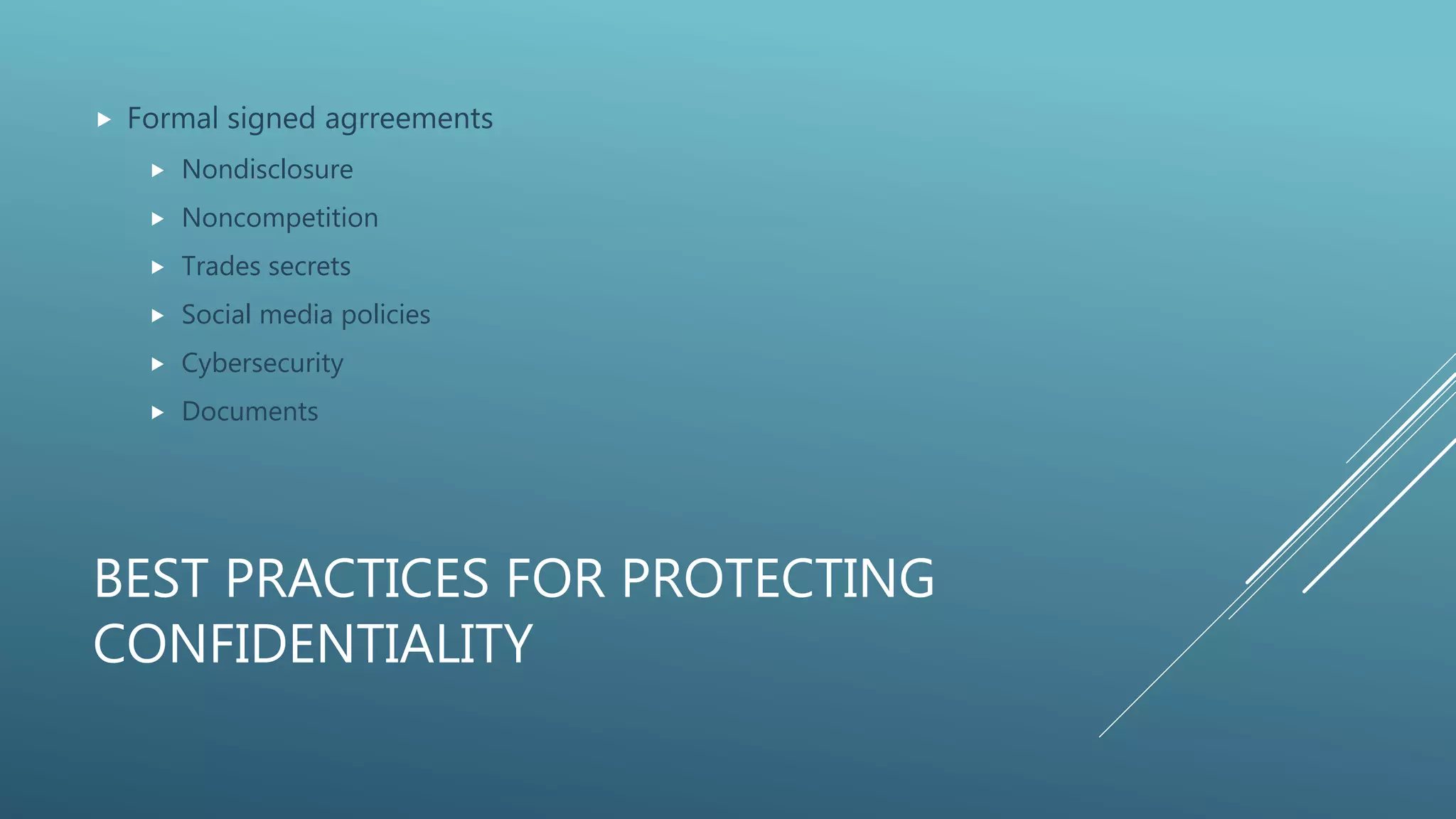
Best Practices for Protecting Confidential Information
The following are essential steps to take to protect confidential information in the workplace: Restricting access to the information Maintaining a register which records developments in confidential information Including appropriate terms in employee, consultant, and other freelancer contracts Encrypting email and documents Implementing an information rights management (IRM) system
Automated Redaction Solutions
Discover how to keep information confidential in the workplace and explore the benefits of automated redaction solutions. For example, if a company has to share confidential information with external parties, such as contractors or vendors, an automated redaction system can scramble or mask sensitive data to prevent unauthorized access.
Document Encryption

Without document encryption, your confidential information is open to theft, leaks, or accidental exposure, especially if you're sending files by email or storing them on shared drives. Even strong access controls can't fully protect content from hackers or insider leaks if the files themselves aren't locked down.
Protecting Personal Information in the Digital Age
Post information about your life sparingly. Avoid personality quizzes and third-party apps that request access to your profile data—many collect information for marketing or malicious purposes. The seemingly harmless details you share online can become ammunition for identity thieves.
LegacyGuard: Trust and Protect Your Business
Protecting your business from competitive threats is vital. Losing a team or a key employee to a competitor can be extremely damaging. LegGuard keeps your legacy private and protected your way. A trust keeps all this private and confidential. Your business strategy stays out of the public eye.
Protect Confidental Business Information with NIST Guidelines
The Department of Commerce has a long and successful track record of protecting confidential information. Additionally, the National Institute of Standards and Technology (NIST) provides guidelines for protecting Controlled Unclassified Information (CUI) resident in nonfederal systems and organizations.
Final Thoughts
Protecting confidential information in the workplace is crucial for security and compliance. With the rise of data breaches and identity theft, businesses must prioritize protecting sensitive data. By restricting access, maintaining a register, and including terms in contracts, businesses can safeguard their confidential information and prevent data breaches.