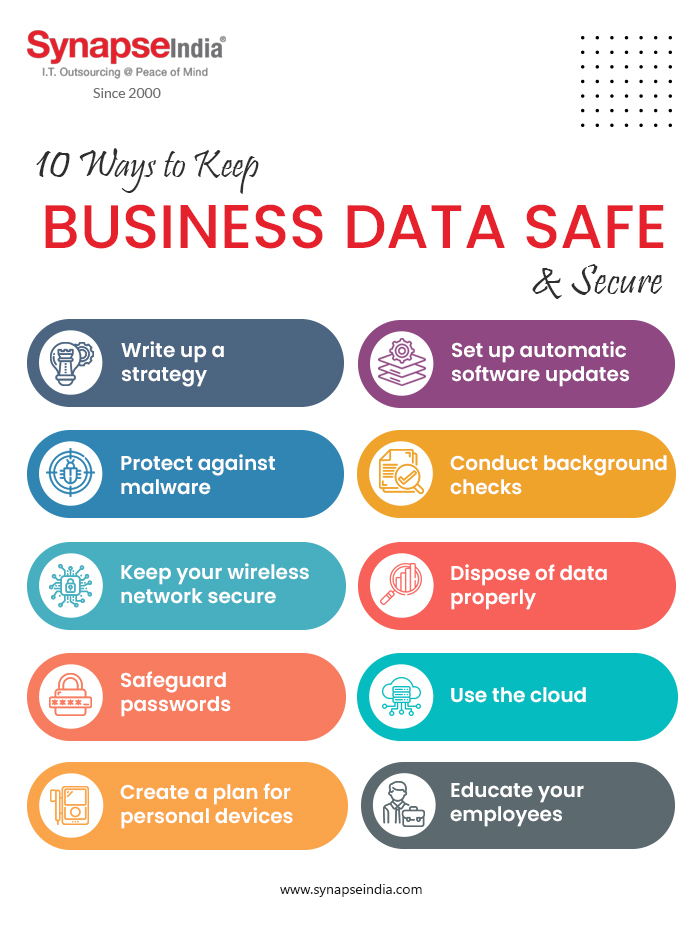
10 Actionable Tips for Protecting Data in the Enterprise
As the world becomes increasingly dependent on digital technologies, the importance of protecting sensitive data in the enterprise cannot be overstated. With the rise of cyber threats, data breaches, and regulatory compliance requirements, organizations must prioritize data security to prevent financial losses, maintain customer trust, and ensure business continuity. In this article, we will provide 10 actionable tips for protecting data in the enterprise, covering best practices for data classification, access controls, encryption, and more. Whether you're a CISO, IT professional, or business leader, these tips will help you safeguard your organization's sensitive information and stay ahead of emerging threats.1. Understand Where Enterprise Data Lives
To protect enterprise data, you must first understand where it lives. This involves conducting a data inventory audit to identify sensitive data across your organization. With this knowledge, you can implement targeted security measures to safeguard critical data, reduce the attack surface, and improve incident response.2. Implement Data Anonymization
Data anonymization is a valuable technique for protecting personal information while maintaining its usefulness for analysis and research. This approach involves removing or masking sensitive data, making it difficult for unauthorized parties to access or exploit. By applying data anonymization, you can reduce the risk of data breaches, comply with regulations, and maintain customer trust.3. Develop a Comprehensive Data Protection Strategy
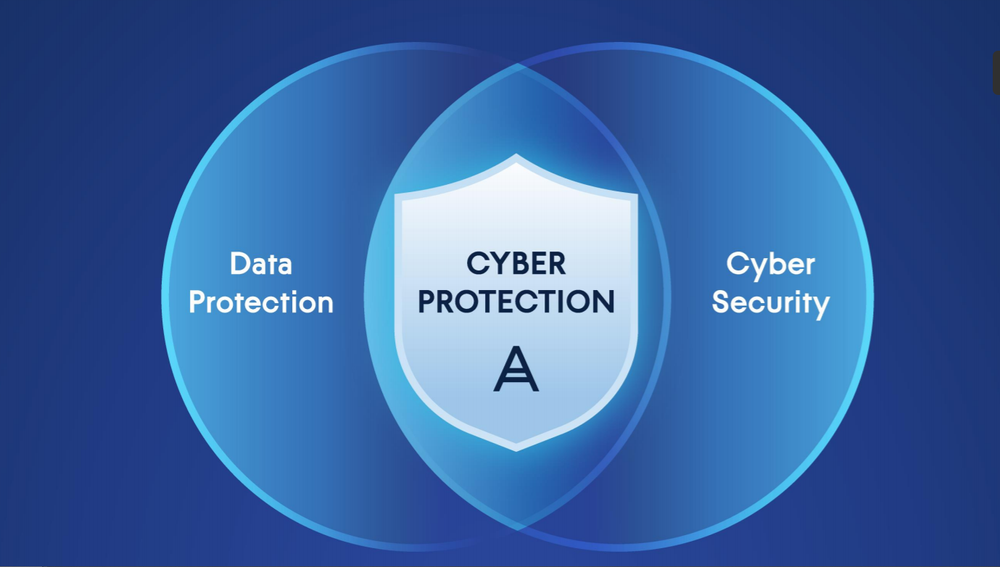
A comprehensive data protection strategy is essential for safeguarding enterprise data in today's hybrid, cloud, and edge environments. This involves implementing multiple layers of security, including encryption, access controls, and collaboration tools. By developing a robust data protection strategy, you can prevent data breaches, ensure regulatory compliance, and maintain business continuity.4. Implement Zero Trust Architecture
Zero trust architecture is a security approach that assumes all users and devices are untrusted, regardless of their location or identity. This involves implementing robust authentication, authorization, and encryption measures to ensure that only authorized parties can access sensitive data. By adopting a zero-trust architecture, you can reduce the risk of data breaches, prevent lateral movement, and improve incident response.5. Classify Data by Sensitivity