Critical Infrastructure from Cyber Threats: A National Priority
May 29, 2024 - The White House recently released National Security Memorandum-22 (NSM) on Critical Infrastructure Security and Resilience, which updates national policy on how the U.S. government protects and secures critical infrastructure from cyber and all-hazard threats.
Understanding the Risks
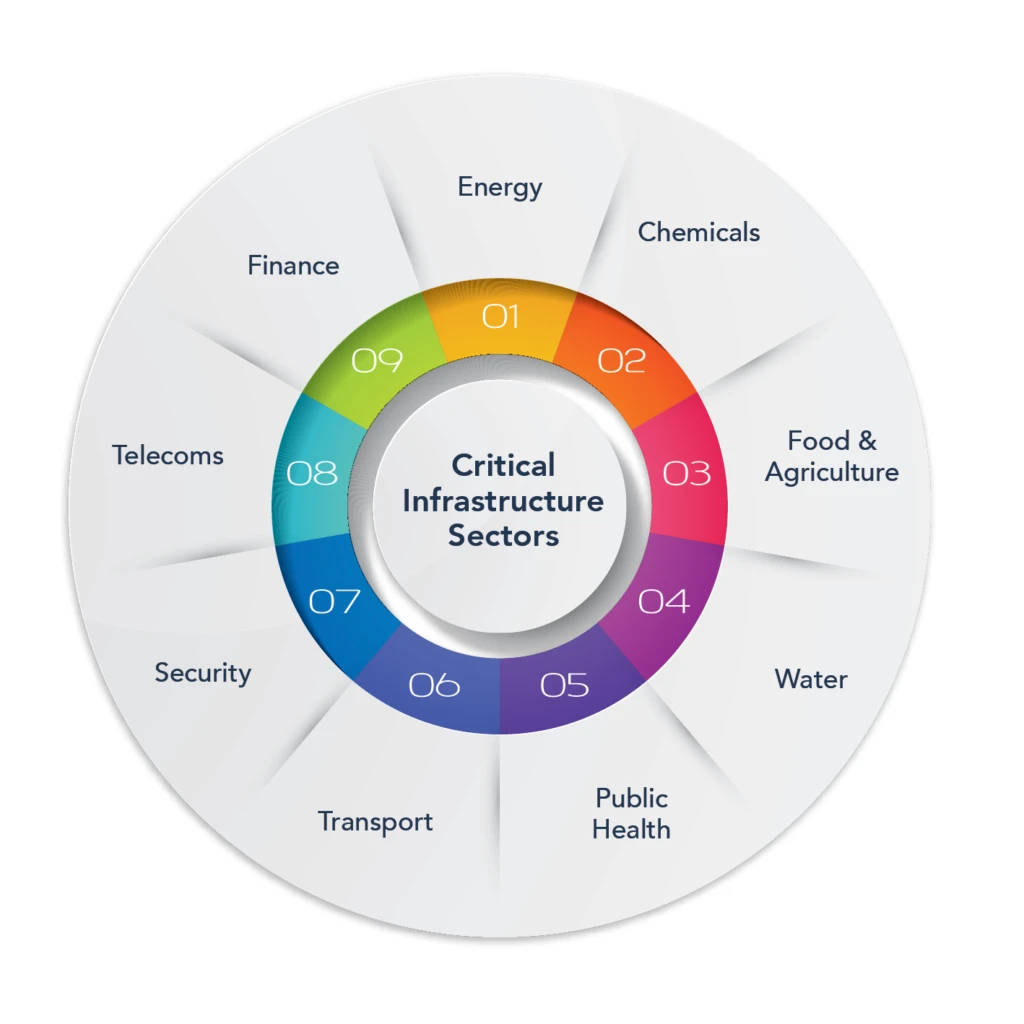
Protecting critical infrastructure - like water and electricity - from cyberattacks is a national priority. Federal agencies and critical infrastructure owners and operators must share information to tackle increasingly complex cyber threats. Long-standing challenges, such as security concerns and timeliness, make this harder.
The Evolving Threat Landscape
- The rise in threats to critical infrastructure reminds us: these are not isolated risks, but connected vulnerabilities, where a single breach can send ripples across the nation's most vital systems.
- A new intelligence report warns that China, Russia, Iran, and North Korea are intensifying cyber operations against U.S. critical infrastructure, while ransomware attacks and threats to satellites expand the digital battlefield.
A Nationwide Effort
CISA offers a range of cybersecurity services and resources focused on operational resilience, cybersecurity practices, organizational management of external dependencies, and other key elements of a robust and resilient cyber framework.
Cybersecurity in the Digital Age
The contemporary geopolitical landscape is increasingly defined by the transition of cyber operations from a tool of clandestine espionage into a primary medium for strategic signaling. In this "post-physical" security environment, critical national infrastructure (CNI) comprising the energy grids, telecommunications networks, maritime ports, and logistics chains that sustain modern society is at risk.
Long-term Vulnerability Reduction Mission Area
Mitigation, build and sustain resilient systems, communities, and critical infrastructure and key resources lifelines so as to reduce their vulnerability to natural, technological, and human-caused threats and hazards by lessening the likelihood, severity, and duration of the adverse consequences.
Real-time Defense Against AI-Speed Threats
Booz Allen's Vellox suite pioneers AI-native cyber defense, combating AI-speed threats to U.S. critical infrastructure and national security.
Protecting Critical Infrastructure from Cyber Threats
The President's Executive Order (EO) on Sustaining Select Efforts to Strengthen the Nation's Cybersecurity and Amending Executive Order 13694 and Executive Order 14144 issued on June 6, 2025, charges multiple agencies - including NIST - to strengthen the nation's cybersecurity by focusing on critical protections against foreign cyber threats and enhancing secure technology practices.
Cyber Threats Don't Take Time Off
Cyber threats don't take time off. As the federal lead for Cybersecurity Awareness Month and the nation's cyber defense agency, the Cybersecurity and Infrastructure Security Agency, or CISA, urges all U.S. small and medium businesses and state, local, tribal, and territorial governments to take one action today to improve their cybersecurity.
Cybersecurity Attacks and Defense
AI is everywhere nowadays and will transform cybersecurity attacks and defense both now and in the near future. The cybersecurity landscape is fundamentally changing as adversaries deploy sophisticated AI agents, redefining cyber-attack economics and dynamics. Especially for critical infrastructure, it is crucial to be protected and resilient.
Real-World Strategies to Protect Critical Water Infrastructure
Join Government Technology, YISDA and the State of Utah's Chief Information Security Officer for a live webinar where we'll share proven, real-world strategies to protect critical water infrastructure quickly, effectively, and without major disruption.
Conclusion
Protecting critical infrastructure from cyber threats is a national priority. As the threat landscape continues to evolve, it's crucial for federal agencies, critical infrastructure owners and operators, and cybersecurity professionals to share information and collaborate to tackle increasingly complex cyber threats.